S3 Bucket Takeover via JavaScript File – Bug Bounty Writeup
Amazon S3 bucket takeovers are a common and impactful vulnerability in web applications. When a JavaScript file references an S3 bucket that no longer exists (but is still expected to serve assets), attackers can claim ownership of that bucket and serve malicious content in its place.

Introduction
AWS S3 bucket takeovers are a common and impactful vulnerability in web applications. When a JavaScript file references an S3 bucket that no longer exists (but is still expected to serve assets), attackers can claim ownership of that bucket and serve malicious content in its place. This is particularly dangerous when the bucket is referenced directly in production JS files used by the frontend.
At Jsmon.sh, our mission is to help organizations secure their JavaScript attack surface. In this case, our research team discovered a misconfigured S3 bucket referenced in a live JS file, which was ripe for takeover.
Vulnerability Summary
- Affected JS File:
https://example.com/pathx/pathy/app.js - Exposed Bucket Reference:
https://<non-existent-bucket>.s3-eu-west-1.amazonaws.com
This JS file directly referenced an S3 bucket that had not been claimed. This meant an attacker could create this bucket in their own AWS account and serve malicious content from it.
Step-by-Step Reproduction
- Visit the JavaScript file:
https://example.com/pathx/pathy/app.js - Search for any string matching
s3.amazonaws.com,s3-<region>.amazonaws.comor similar S3 bucket patterns. - We found a link to a bucket like:
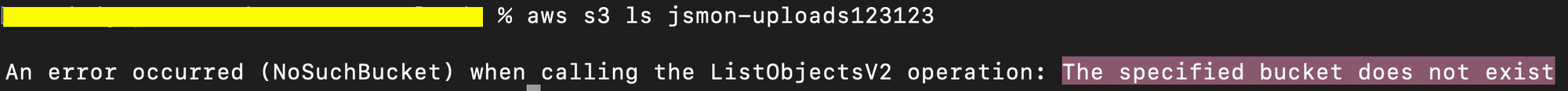
https://<non-existent-bucket>.s3-eu-west-1.amazonaws.com - On verifying via AWS, the bucket name was unclaimed.
Our researcher successfully registered this S3 bucket. - We uploaded a harmless
index.htmlfile to prove control. - Since the JS file relies on this bucket for loading content, anyone accessing the app would unknowingly load data served from our controlled bucket.
Impact
By taking over the S3 bucket, we gained full read/write access to it. This allowed:
- Uploading malicious JS/CSS files that would be loaded by clients.
- Serving phishing pages or malware under the legitimate domain context.
- Potential redirection or manipulation of frontend behavior.
Since this bucket was tied to the production JavaScript file, it directly impacted users and was escalated to High severity (8.6).
Timeline
| Date | Event |
|---|---|
| 07 Mar 2025 | Reported to the security team |
| 13 Mar 2025 | Triaged by program |
| 14 Mar 2025 | Severity changed from Medium to High |
| 26 Jun 2025 | $250 Bounty awarded to Jsmon.sh team |

Jsmon In Action
Our security research team leveraged Jsmon.sh to scan bug bounty program assets for potential S3 bucket takeover vulnerabilities. By simply scanning a domain or a JavaScript file URL, Jsmon's JS Intelligence engine automatically flags exposed or unclaimed S3 buckets referenced in the code making it easy to identify takeover opportunities at scale.
Conclusion
S3 bucket takeovers remain a critical security issue, especially when exposed through JavaScript files. This case highlights how attackers can abuse forgotten or misconfigured cloud resources referenced in frontend code.
If you're a bug bounty hunter, always inspect JS files for asset URLs, especially anything on s3.amazonaws.com. And if you’re a developer, avoid referencing deprecated or unmonitored buckets in your production code.
How We Can Help?
In 2026, Security tooling must deliver context—not just alerts. Jsmon continuously maps and monitors your JavaScript and web attack surface, identifying real risks like exposed endpoints, leaked secrets, misconfigurations, and client-side vulnerabilities as they emerge.
By combining context-aware analysis with continuous monitoring, Jsmon dramatically reduces false positives and helps teams focus on issues that are actually exploitable.
Secure your attack surface in real time with Jsmon.
Stay safe and keep hunting!
— The Jsmon.sh



