ethical hacking
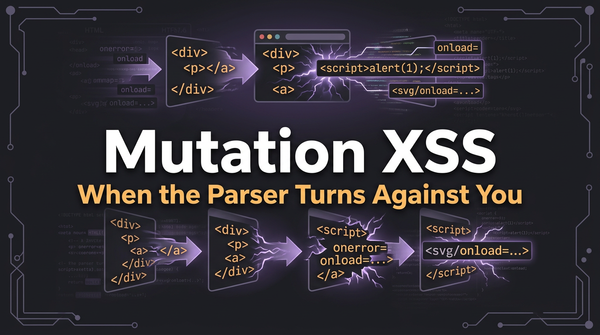
What is Mutation XSS (mXSS)? Ways to Exploit, Examples and Impact
Discover how Mutation XSS (mXSS) works, why it bypasses sanitizers, and real-world examples. Learn to secure your web apps with Jsmon's guide.
ethical hacking
Discover how Mutation XSS (mXSS) works, why it bypasses sanitizers, and real-world examples. Learn to secure your web apps with Jsmon's guide.
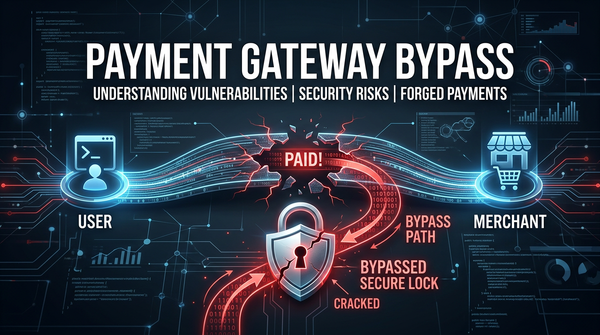
googlepay
Learn how to identify and prevent payment gateway bypass vulnerabilities including parameter tampering and webhook spoofing in this technical guide.
ethical hacking
Discover how Browser Cache Poisoning works, its impact on user security, and technical ways to exploit and prevent this persistent web vulnerability.

cybersecurity
In the modern era of web browsing, real-time communication has become a standard expectation. Whether you are jumping into a video conference, playing a multiplayer game, or sharing files directly between browsers, technology like WebRTC makes these seamless experiences possible. However, this convenience comes with a significant security trade-off known
api security
Discover how certificate pinning bypass works, common exploitation tools like Frida, and the impact of broken SSL pinning on mobile application security.

cybersecurity
Portable Document Format (PDF) files are the universal standard for sharing documents across different platforms while maintaining consistent formatting. From invoices and bank statements to whitepapers and legal contracts, PDFs are everywhere. However, beneath their static appearance lies a complex internal structure that can be manipulated by attackers. PDF Injection
403 bypass
Learn what root detection bypass is, how it works, and common exploitation methods like Frida and Smali patching in this technical cybersecurity guide.
cybersecurity
Excel Formula Injection, also known as CSV Injection, is a prevalent yet frequently overlooked security vulnerability that occurs when an application improperly handles user-supplied input that is later exported into a spreadsheet file. While many developers focus on preventing SQL Injection or Cross-Site Scripting (XSS), they often forget that data
403 bypass
Learn how Application Layer DoS attacks work, explore common exploitation techniques like Slowloris, and discover how to mitigate Layer 7 threats effectively.
ethical hacking
Discover the risks of Wildcard CORS origins. Learn how attackers exploit reflected origins and how to secure your API against data exfiltration.

403 bypass
Learn how BLE spoofing works, technical exploit methods, and real-world impacts on IoT security. Discover how to protect your organization's attack surface.
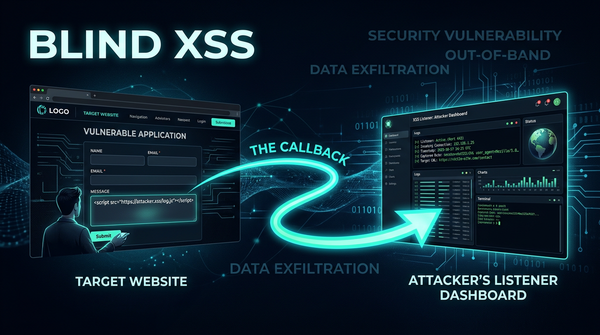
ethical hacking
Learn how Blind XSS works, common exploit examples, and impact. Discover how to detect and prevent this dangerous out-of-band vulnerability today.