What is MIME Type Bypass? Ways to Exploit, Examples and Impact
Learn how to detect and prevent MIME Type Bypass vulnerabilities. Explore Magic Bytes, header manipulation, and secure file upload best practices.
Learn how to detect and prevent MIME Type Bypass vulnerabilities. Explore Magic Bytes, header manipulation, and secure file upload best practices.

Understand coupon code abuse techniques like race conditions and brute forcing. Learn technical mitigation strategies to protect your e-commerce platform.

Learn how race conditions allow coupon abuse. This technical guide covers exploitation, real-world examples, and prevention for secure e-commerce apps.
cybersecurity
Explore common Kubernetes misconfigurations, technical exploit examples, and how to protect your infrastructure. Learn to secure your K8s clusters today.

403 bypass
Learn how to identify, exploit, and prevent insecure data storage in mobile apps. A technical guide for Android and iOS security beginners.
403 bypass
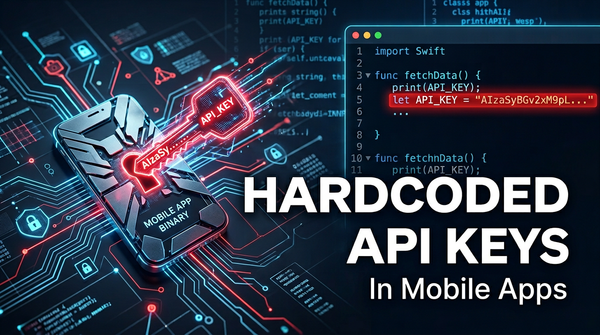
Discover the dangers of hardcoded API keys in mobile apps. Learn how attackers exploit them and how to secure your infrastructure with Jsmon.
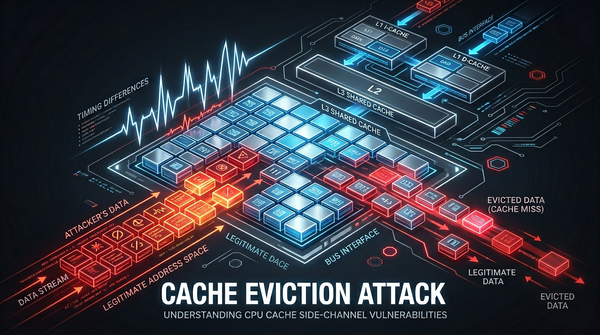
cache eviction
Discover how cache eviction attacks like Prime+Probe work. Learn to identify, exploit, and prevent these side-channel vulnerabilities in modern hardware.
cybersecurity
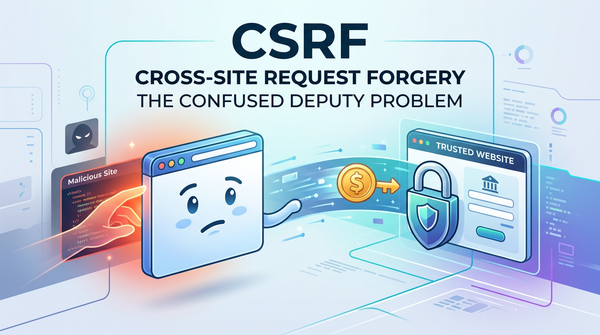
Understand Cross-Site Request Forgery (CSRF) with technical examples and payloads. Learn how to defend your web applications using modern security practices.

api security
Master the technical details of deeplink hijacking. Learn how attackers exploit mobile URI schemes and how to protect your app's data from exposure.

cybersecurity
Explore AWS IAM privilege escalation techniques, payloads, and impacts. Learn how to secure your AWS environment against identity-based attacks.
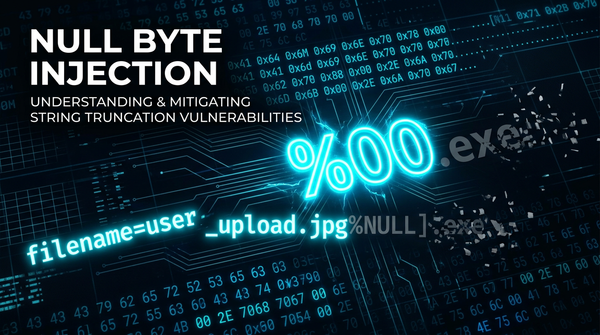
nullByte
Learn how Null Byte Injection exploits file upload vulnerabilities. Discover technical examples, bypass techniques, and how to secure your infrastructure.
api security
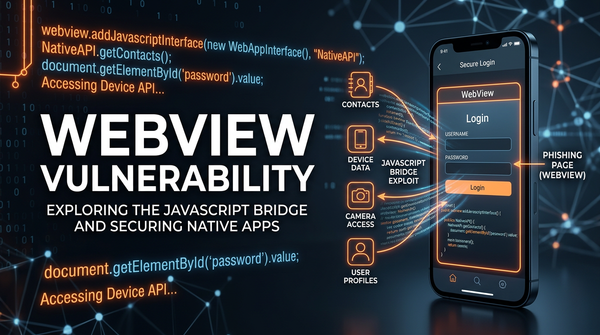
Learn how WebView vulnerabilities like JS Bridge injection and file access work. Explore technical examples, security risks, and mitigation tips for mobile apps.