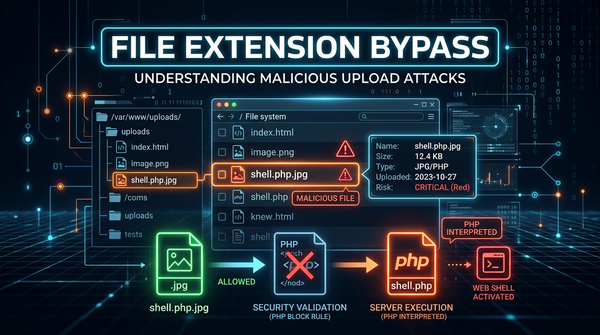
What is File Extension Bypass? Ways to Exploit, Examples and Impact
Learn how attackers bypass file extension filters to achieve RCE. Explore common bypass techniques and mitigation strategies to secure your web applications.
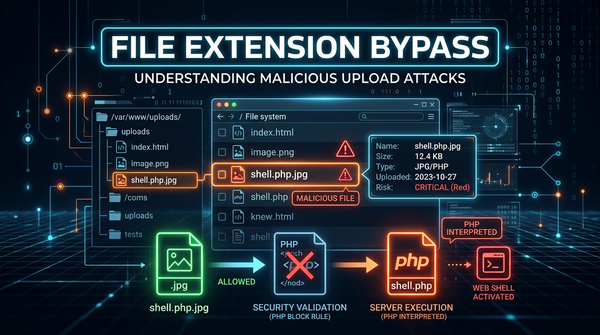
Learn how attackers bypass file extension filters to achieve RCE. Explore common bypass techniques and mitigation strategies to secure your web applications.

Learn how Zip Slip allows RCE via path traversal in archive extraction. See technical examples and learn how to secure your code against this critical flaw.
ethical hacking
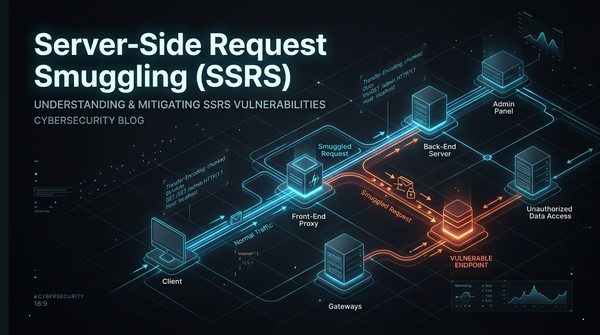
In the modern landscape of web architecture, applications are rarely standalone entities. They typically sit behind a chain of servers, including load balancers, reverse proxies, and content delivery networks (CDNs). While this multi-tiered approach improves performance and scalability, it introduces a dangerous class of vulnerability known as Server-Side Request Smuggling
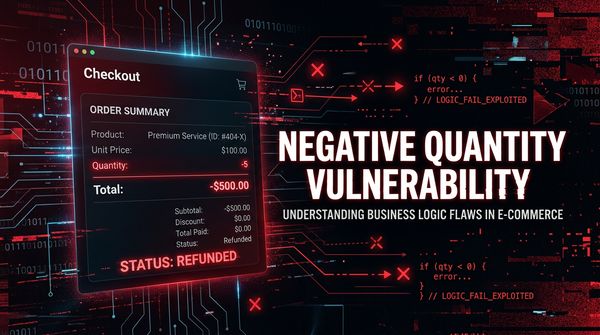
Learn how negative quantity vulnerabilities allow attackers to manipulate e-commerce totals. Explore exploit examples, technical impacts, and prevention tips.
cybersecurity
Internet Message Access Protocol (IMAP) is a foundational technology that allows email clients to communicate with mail servers. While it has been around for decades, it remains a critical part of our digital infrastructure. However, like many protocols that rely on text-based commands, it is susceptible to a specific class
Learn how Pixel Flood attacks exploit image processing to cause DoS. Explore exploitation techniques, real-world examples, and mitigation strategies.

Learn how price manipulation vulnerabilities work, explore real-world exploitation examples, and discover best practices for securing e-commerce platforms.
403 bypass
Learn how the XML Bomb (Billion Laughs) attack works, explore exploitation examples, and find technical ways to prevent this resource exhaustion vulnerability.

Discover how ImageTragick (CVE-2016-3714) works. Learn to exploit and mitigate RCE in ImageMagick with practical examples and security best practices.
Learn how carding attacks work, how attackers use bots to validate stolen cards, and technical ways to protect your business from e-commerce fraud.

403 bypass
Learn what Intent Injection is in Android, how to exploit it with code examples, and how to secure your mobile applications against these vulnerabilities.

cybersecurity
Docker has revolutionized the way we develop, ship, and run applications by providing a lightweight, portable environment called a container. However, the very nature of containers—sharing the host machine's OS kernel—introduces unique security challenges. A Docker container breakout, also known as a container escape, occurs when