
cybersecurity
What is Redis Unauthenticated Access? Ways to Exploit, Examples and Impact
Explore how Redis unauthenticated access leads to RCE and data theft. Learn exploitation methods like SSH injection and critical security mitigations.

cybersecurity
Explore how Redis unauthenticated access leads to RCE and data theft. Learn exploitation methods like SSH injection and critical security mitigations.

cybersecurity
Cross-Site Search (XS-Search) is a sophisticated class of side-channel vulnerabilities that allows an attacker to exfiltrate sensitive information from a web application by abusing search functionality. While traditional web vulnerabilities like SQL Injection or Cross-Site Scripting (XSS) involve direct data theft or code execution, XS-Search is more subtle. It falls

cybersecurity
Learn how Blind SSRF works, how to detect it using OAST, and ways to prevent this critical vulnerability from exposing your internal network.

cybersecurity
Discover how Firebase database misconfigurations lead to data leaks. Learn to identify insecure rules, exploit scenarios, and prevention tips.
cybersecurity
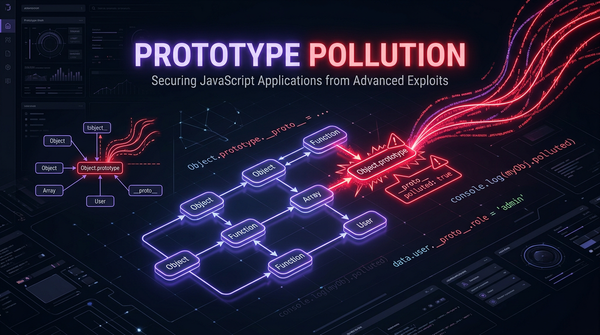
JavaScript is a language built on the foundation of prototypes. While this provides incredible flexibility and efficiency in memory management, it also introduces a unique class of vulnerabilities known as Prototype Pollution. This vulnerability becomes particularly dangerous when combined with "gadgets"—pre-existing code snippets within an application that,

cybersecurity
Master Server-Side Request Forgery (SSRF). Learn how attackers bypass filters, access cloud metadata, and secure your infrastructure against SSRF attacks.
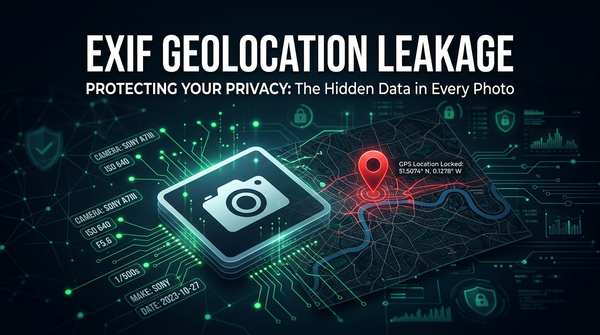
Learn how EXIF metadata leaks GPS data. Explore extraction tools like ExifTool and Python, real-world examples, and mitigation strategies for security.
cybersecurity
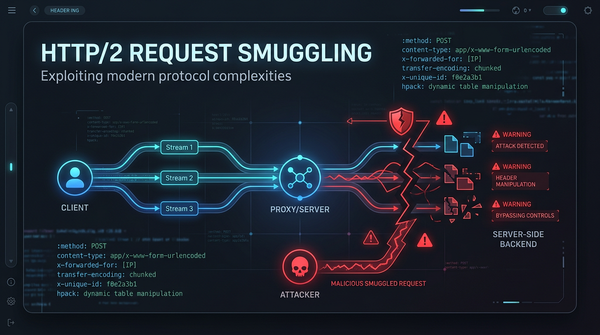
As the web evolved, the limitations of the aging HTTP/1.1 protocol became apparent. To address latency and performance issues, HTTP/2 was introduced, bringing features like binary framing, multiplexing, and header compression. However, with new features come new security challenges. HTTP/2 Request Smuggling has emerged as a

403 bypass
Discover how side-channel attacks exploit physical leakage to steal data. Learn about timing attacks, power analysis, and mitigation strategies.

Explore unrestricted file upload vulnerabilities. Learn how attackers use web shells and XSS to compromise servers and how to implement robust security.
cybersecurity
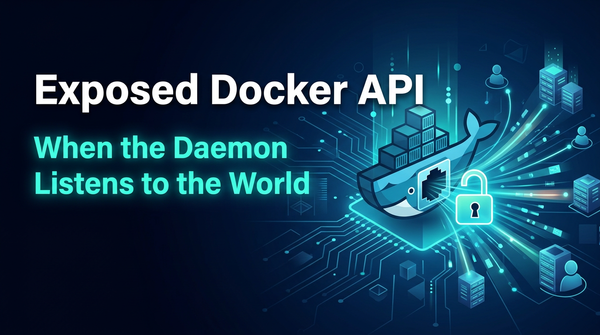
Learn how exposed Docker APIs lead to host compromise. Explore exploitation examples, RCE techniques, and security best practices to protect your servers.

Learn about currency rounding vulnerabilities (salami slicing). See how rounding errors lead to financial loss and how to secure your code.