cybersecurity
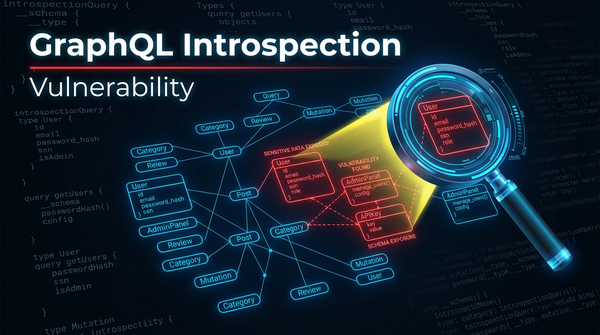
What is GraphQL Introspection Vulnerability? Ways to Exploit, Examples and Impact
Understand GraphQL introspection risks, exploitation techniques, and mitigation steps. Secure your API schema from information disclosure today.
cybersecurity
Understand GraphQL introspection risks, exploitation techniques, and mitigation steps. Secure your API schema from information disclosure today.
cybersecurity
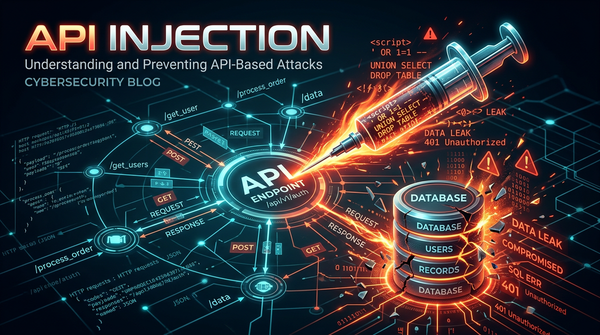
Master the fundamentals of API Injection. Explore technical examples of SQLi, NoSQLi, and Command Injection, and learn how to secure your API endpoints.
cybersecurity
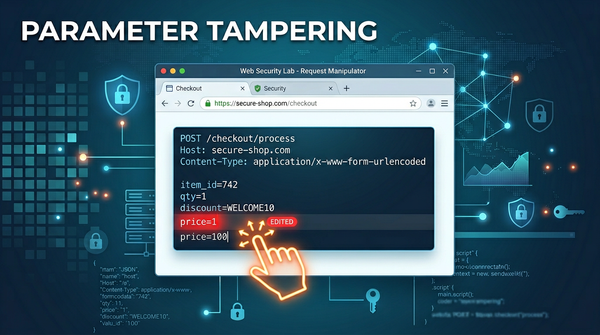
Learn how parameter tampering works, see real-world exploitation examples, and discover how to prevent this critical web vulnerability.
cybersecurity
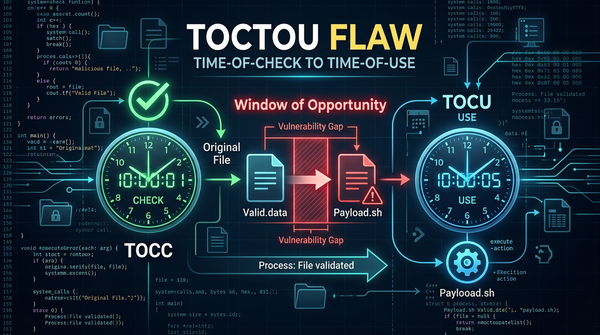
Discover how Time-of-Check to Time-of-Use (TOCTOU) flaws create race conditions. Learn to identify, exploit, and mitigate these vulnerabilities in your code.
cybersecurity
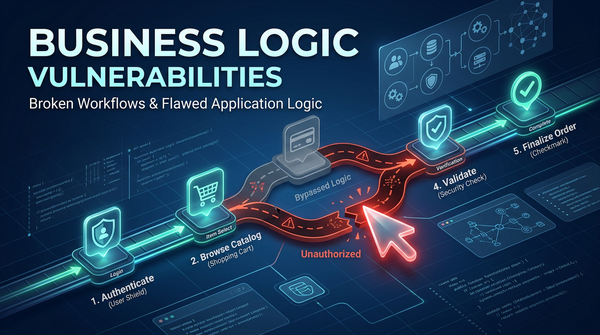
Discover common business logic flaws, real-world exploit examples, and prevention strategies to secure your web applications against logical attacks.

cybersecurity
Master the risks of Improper Assets Management and Shadow APIs. Learn how attackers exploit undocumented endpoints and how to protect your infrastructure.

cybersecurity
Deep dive into Rate Limiting and Resource Exhaustion. Learn technical exploitation, bypass techniques, and how to secure your APIs against automated attacks.

cybersecurity
Learn how to identify and prevent Excessive Data Exposure in APIs. Explore technical examples, exploitation methods, and security best practices.
cybersecurity
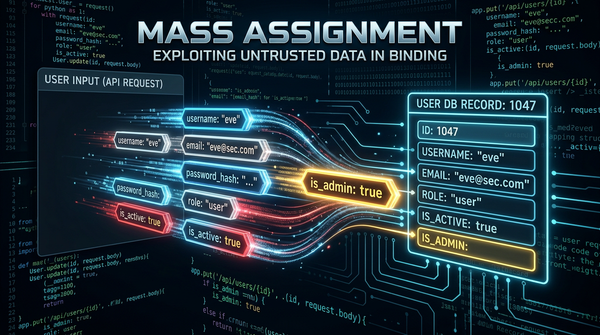
Learn how Mass Assignment vulnerabilities allow attackers to escalate privileges. Explore technical examples and mitigation strategies for secure APIs.

cybersecurity
Learn about Broken Function Level Authorization (BFLA), its impact, and how to prevent this critical API security flaw with technical examples and best practices.
cybersecurity
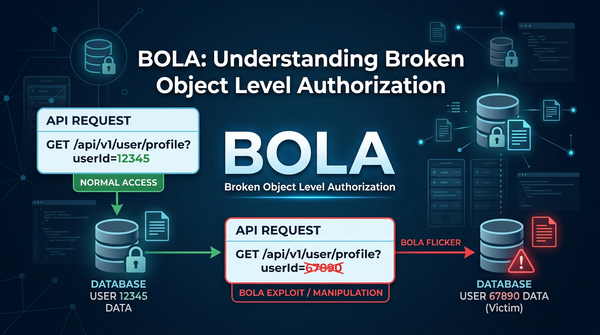
Master Broken Object Level Authorization (BOLA). Learn technical exploitation methods and how to secure your APIs against the #1 OWASP threat.
cybersecurity
Learn how cryptographic failures happen, explore technical exploit examples, and discover best practices for securing sensitive data in this deep dive.