How to Bypass WAFs Using Payload Padding and Inspection Limits
Learn how to bypass WAFs using payload padding across major firewall providers, waf evasions, and tools.
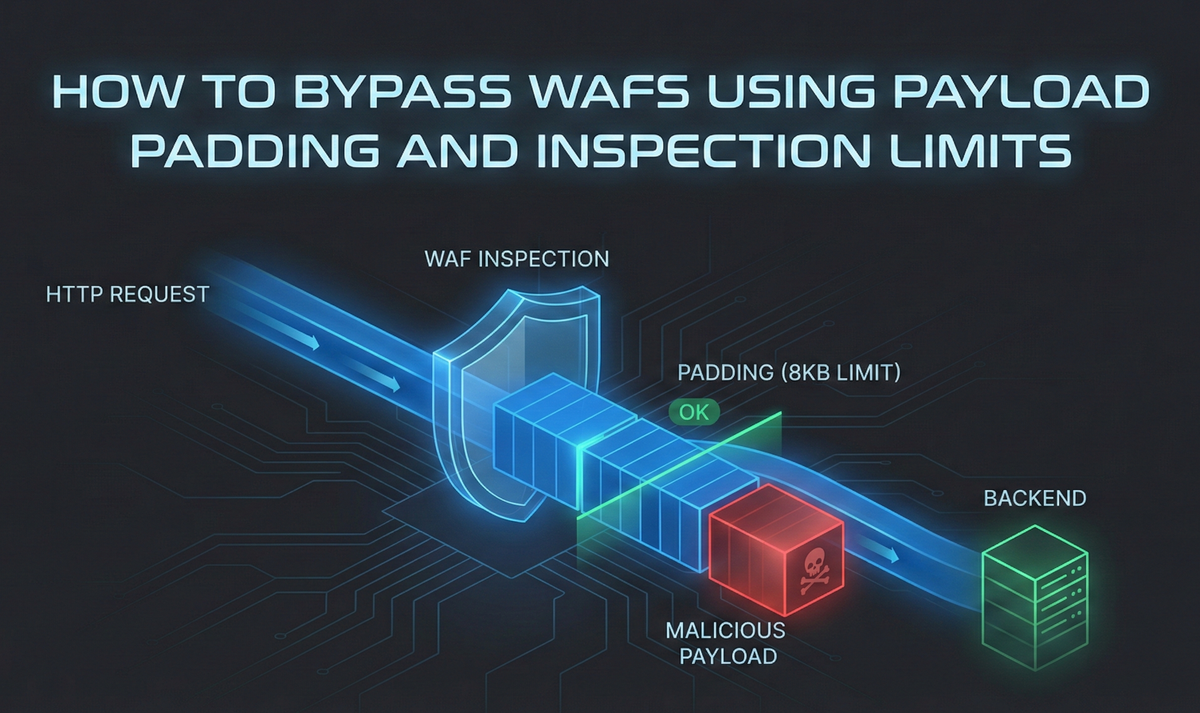
Payload padding exploits a practical constraint in many Web Application Firewalls (WAFs): to preserve latency and throughput, they often inspect only the first N kilobytes of an HTTP request body. By placing benign “junk” content up front and moving the malicious payload past that inspection boundary, an attacker can cause the WAF to approve the request while the origin application still processes the full body.
This article explains the concept, highlights common inspection limits across major providers, walks through reliable padding techniques for JSON, XML, and form-encoded requests, and closes with clear defensive guidance so teams can fail safely instead of failing open.
Introduction to WAF Payload Padding Attacks
WAFs are commonly treated as the “last line” that stops SQL injection, XSS, and other high-impact attacks. In practice, many modern bypasses do not rely on clever encoding tricks. They rely on understanding where security tooling makes trade-offs.
One of the most important trade-offs is performance vs. depth of inspection. WAFs sit inline. They must make fast decisions on every request, including requests that may legitimately carry large bodies such as file uploads and large JSON payloads.
At some point, inspecting an entire body becomes too expensive.
Understanding WAF Request Body Inspection Limits
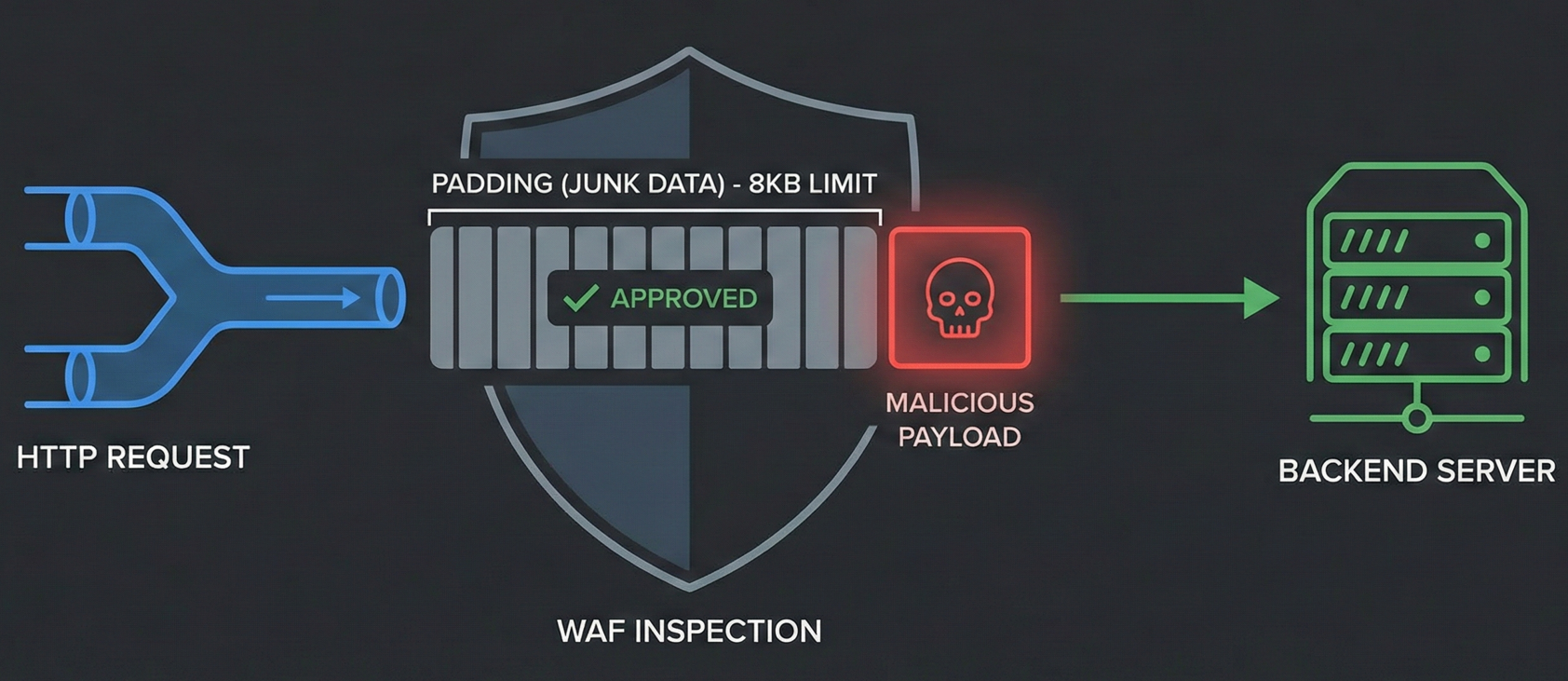
Most WAF engines buffer a portion of the request body in memory so they can apply signature checks and rules. But fully parsing and scanning very large bodies can be costly in CPU and memory and can introduce user-facing latency.
To keep systems responsive, many WAFs implement a request body inspection limit.
Why Do WAFs Limit Request Body Sizes?
Blocking every “large” request is usually not viable.
- Applications often need large requests for uploads, bulk operations, and rich API calls.
- Organizations often prioritize availability and user experience.
- Vendors ship safe defaults for performance, not necessarily for strict security.
The result is a common pattern: inspect the first X KB and allow the rest to pass.
How Attackers Exploit WAF Inspection Limits
If the WAF only inspects the first X bytes, then an attacker can:
- Fill the first X bytes with harmless padding.
- Place the real payload immediately after the cutoff.
The WAF sees only the padding and allows the request.
The origin application (Node.js, Python, Java, PHP, etc.) still parses the entire body and reaches the malicious portion.
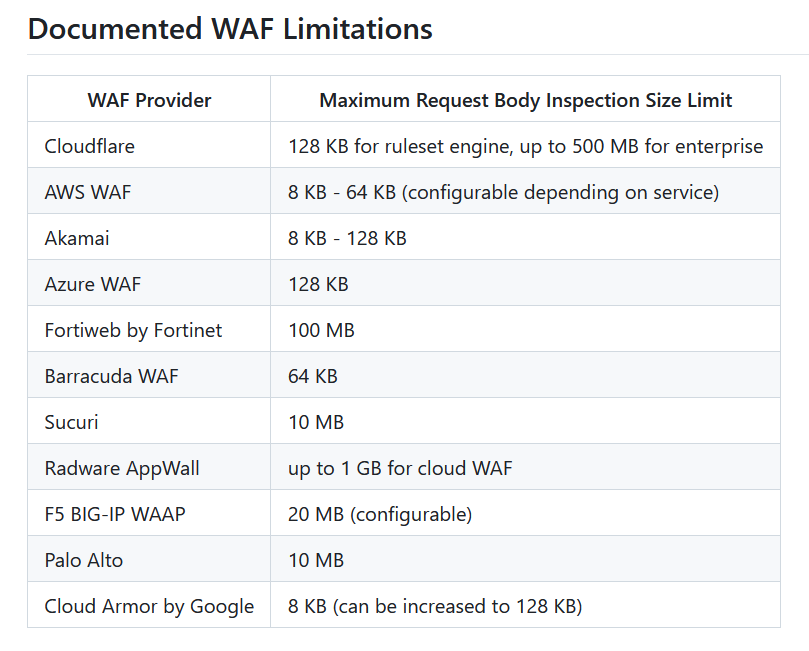
Common WAF Body Inspection Limits by Provider
Knowing typical inspection boundaries helps you test systematically.
AWS WAF
AWS WAF limits vary by where it is attached:
- ALB and AWS AppSync: hard 8 KB (8,192 bytes) body inspection.
- CloudFront, API Gateway, Cognito, App Runner, Verified Access: default 16 KB, often configurable up to 64 KB (in 16 KB increments).
Akamai
- Common default inspection limit is 8 KB.
- Some deployments can increase this (up to 128 KB in certain configurations), but many real-world environments remain near default settings.
Cloudflare
- Common default is 128 KB for ruleset inspection.
- Enterprise can inspect significantly larger bodies (reported up to hundreds of MB).
Azure WAF
- Common default is 128 KB.
The practical takeaway: 8 KB and 16 KB are high-value first guesses, especially during bug bounty and black-box assessments.
Payload Padding Techniques for WAF Bypasses
Padding is simple in principle, but reliability depends on one thing: the backend parser must remain happy long enough to reach the malicious portion.
That means the padding must be context-aware. Random bytes can break JSON parsers, XML parsers, or form decoding.
Technique A: JSON padding (REST and JSON APIs)
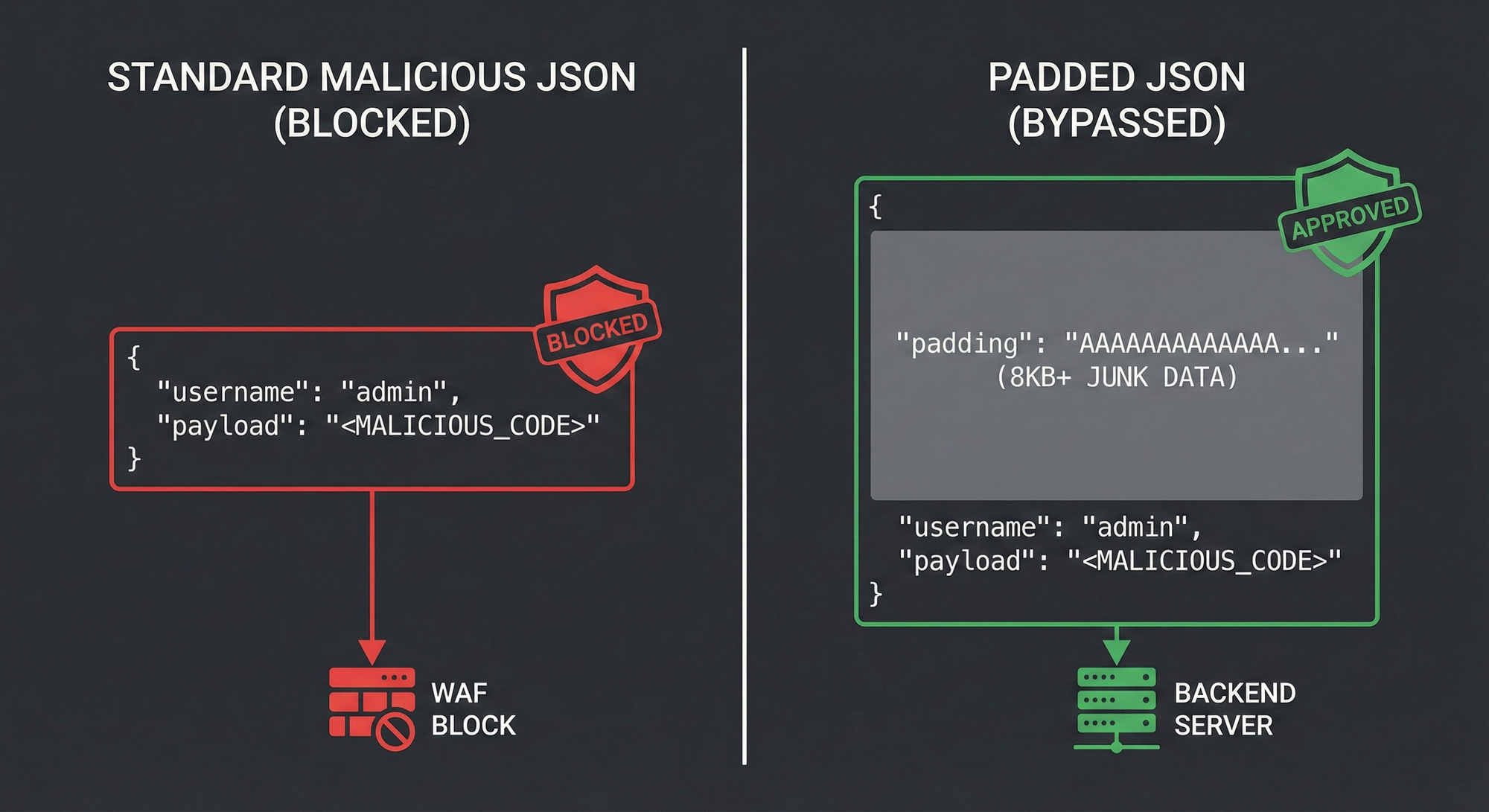
For application/json, create an early key that contains your padding. Place the real exploit field after it.
{
"junk_padding": "A".repeat(8192),
"username": "admin' OR 1=1--",
"password": "password123"
}
Why it works:
- The first 8 KB is dominated by harmless “A” characters.
- The WAF inspects only that portion.
- The application parses the full object and reaches the injection string.
Common Pitfalls and Edge Cases
- Some servers enforce maximum JSON size.
- Some frameworks normalize or reorder fields.
- Some WAFs apply JSON-aware parsing and may inspect more deeply when the body is parseable.
Technique B: XML padding (SOAP and XML parsers)
For XML, padding can be introduced using comments or large benign nodes early in the document.
<!-- A very large benign XML comment repeated until the desired size -->
<user>
<username>admin' OR 1=1--</username>
</user>
Why it works:
- XML comments are ignored by many parsers.
- You can push the real payload deeper without breaking structure.
Technique C: form-encoded padding (classic web forms)
For application/x-www-form-urlencoded, add a “padding” parameter before the sensitive parameters.
POST /login HTTP/1.1
Content-Type: application/x-www-form-urlencoded
padding_data=[8KB_of_junk]&username=<script>alert(1)</script>
Key point: parameter order matters in many WAF implementations and sometimes in application logic. The safest approach is to keep the padding field first.
Technique D: Multipart boundary padding (File uploads)
For endpoints accepting multipart/form-data, WAF inspection limits are incredibly common because parsing large files in-line is a massive performance bottleneck. You can bypass the WAF by injecting a massive, benign text file before the actual malicious parameter.
POST /upload HTTP/1.1
Content-Type: multipart/form-data; boundary=----WebKitFormBoundary
------WebKitFormBoundary
Content-Disposition: form-data; name="junk_file"; filename="junk.txt"
Content-Type: text/plain
[... 8KB to 128KB of 'A's ...]
------WebKitFormBoundary
Content-Disposition: form-data; name="payload"
<script>alert(1)</script>
------WebKitFormBoundary--- File upload endpoints are frequently granted higher WAF size limits or exceptions by administrators.
- The WAF exhausts its memory buffer inspecting the benign
junk.txtfile and allows the rest of the request, including the maliciouspayloadparameter, to pass through uninspected.
Bypassing WAFs using Chunked Transfer Encoding
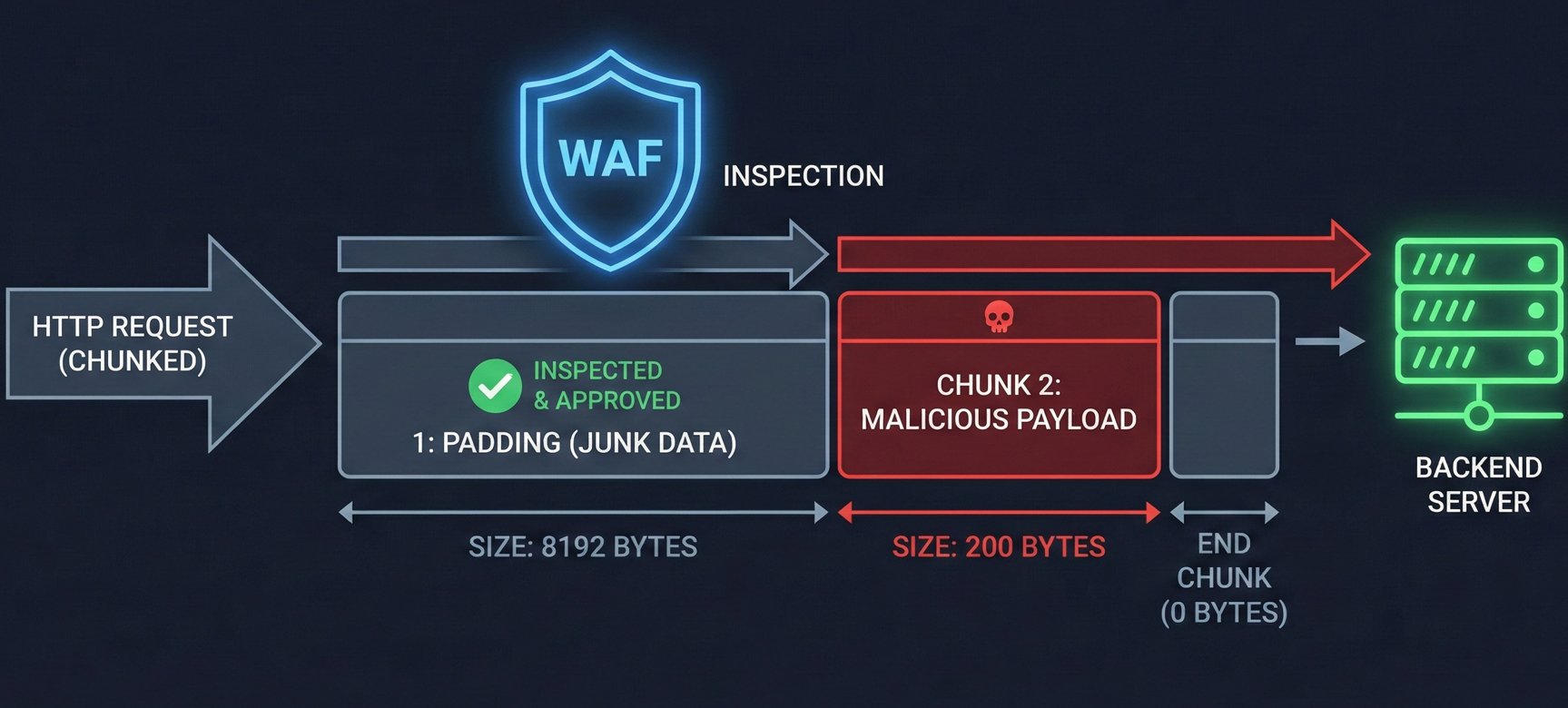
Padding becomes exponentially more dangerous when combined with protocol-level obfuscation like Transfer-Encoding: chunked.
POST /api/submit HTTP/1.1
Transfer-Encoding: chunked
Content-Type: application/json
2000
{"junk_padding": "[8192 bytes of 'A's]", "next": "
40
", "payload": "admin' OR 1=1--"}
0
Why it works:
- Some WAFs struggle to track byte limits accurately when the body is sent in arbitrary chunks.
- If the WAF only inspects the first chunk before giving up or miscalculating the boundary, the backend server will seamlessly reassemble the chunks and execute the payload.
WAF Evasion via HTTP Desync and Parser Confusion
Padding isn't just about exhausting size limits; it can also be used to exploit parser differences between the WAF and the origin server (a form of HTTP Request Smuggling).
Why it works:
- If you inject your padding using unexpected character encodings (like UTF-16) or Unicode anomalies, the WAF might parse the padding differently than the backend.
- The WAF might read a null byte or an invalid UTF-8 sequence inside your padding and stop inspecting early, assuming the request is truncated. Meanwhile, the backend database (which might be more tolerant or use a different default encoding) parses the padding perfectly and processes your trailing exploit.
Tool for Automating WAF Payload Padding Attacks
Manually inserting thousands of characters is slow and error-prone. Tooling exists specifically to streamline this attack path.
nowafpls (Assetnote)
nowafpls is a Burp Suite extension designed for padding-based WAF bypass testing.
What it does well:
- Detects context (JSON, XML, URL-encoded).
- Inserts the right padding structure automatically.
- Lets you choose the padding size (8 KB, 64 KB, 128 KB, etc.) from within Burp Repeater.
Advanced Infrastructure-Level WAF Bypass Methods
In the real world, you may face WAF behavior that is not purely signature-based blocking. Recon traffic can trigger aggressive rate limiting, temporary bans, or long-lived IP reputation hits.
When that happens, padding solves one problem (inspection depth), but not another (traffic controls).
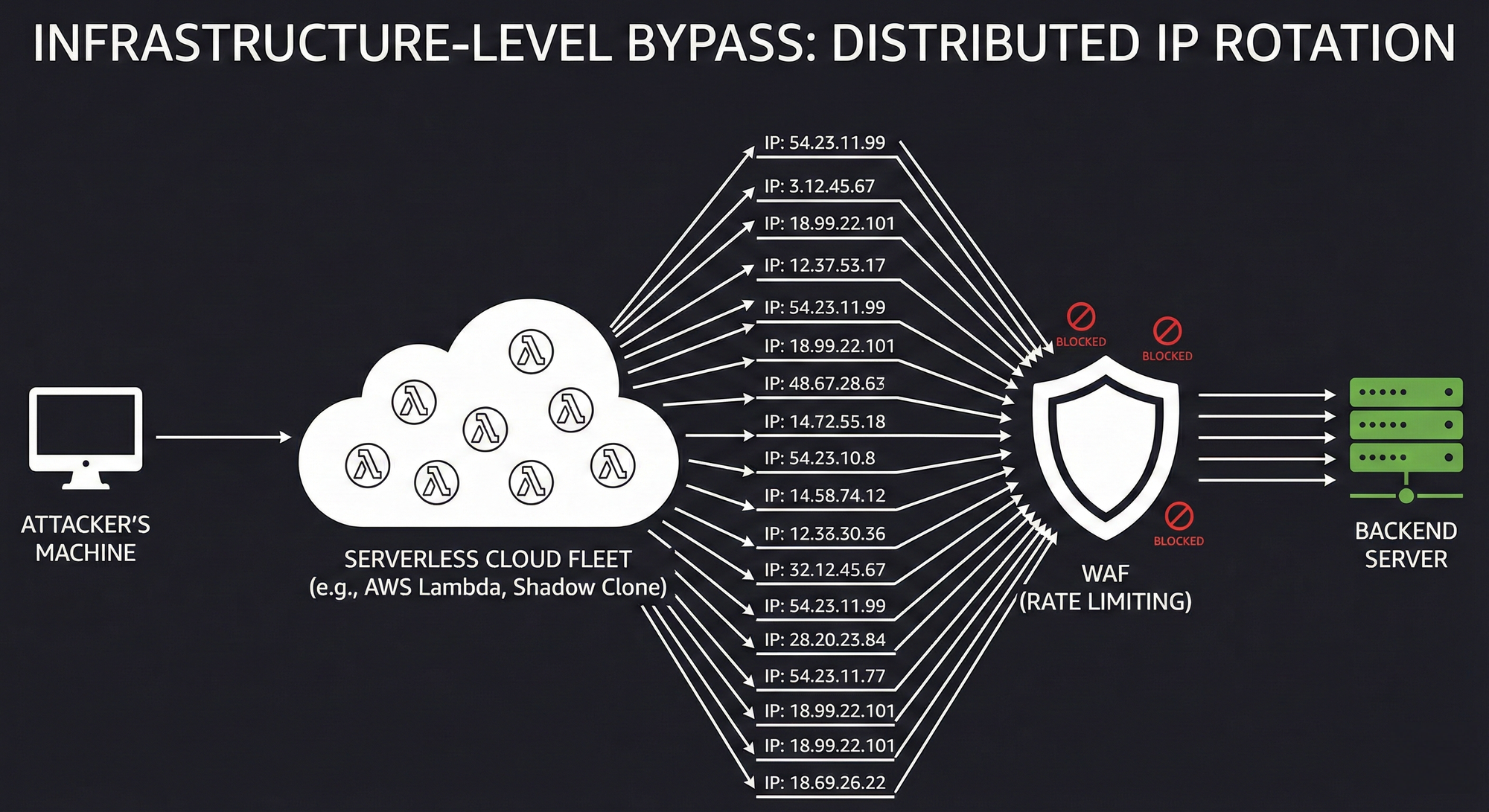
Shadow Clone (serverless distribution)
Shadow Clone uses serverless compute (for example, AWS Lambda or Azure Functions) to distribute requests at scale.
Why it matters:
- Many serverless platforms provide generous free tiers.
- Requests can originate from a large, rotating pool of IP addresses.
- Rate limits tied to a single source IP become much less effective.
Fireprocs (rotating via API Gateway)
Fireprocs generates ephemeral AWS API Gateway endpoints that can naturally cycle through large IP pools.
Typical use case:
- Route Burp Suite / Intruder traffic through the gateway.
- Reduce the impact of IP-based blocking.
“WAF via WAF” (origin exposure and misconfiguration)
If an organization uses a CDN/WAF (for example, Cloudflare) but does not enforce authenticated origin pulls, the origin may be reachable directly.
A high-level version of the pattern:
- Discover the origin IP.
- Proxy the origin through your own CDN/WAF configuration.
- Lower or disable your security settings.
- Send traffic that appears to originate from trusted CDN IP space.
This is not a padding technique, but it highlights the same theme: security controls often depend on infrastructure configuration, not just signatures.
How to Prevent Payload Padding WAF Bypasses
Defenders can address this risk without breaking core application functionality.
Fail closed on oversize bodies
If your WAF supports oversize handling modes, configure it so that requests exceeding the inspection limit are blocked rather than passed through.
This is the single most important fix because it removes the “inspect a little, allow the rest” failure mode.
Increase inspection limits where feasible
If the platform allows it, raise the inspection boundary.
- For AWS services that permit it, move from 16 KB toward 64 KB as appropriate.
Be aware that deeper inspection can increase cost and latency. Treat it as a risk management decision and validate performance impact.
Use endpoint-specific policy instead of one global rule
Many applications only need large bodies in a few places (for example, /upload).
A more resilient policy model:
- Allow larger bodies only where needed.
- Apply stricter body-size and inspection rules everywhere else.
Understanding WAF Limitations and Defense in Depth
Even with perfect WAF settings, you still need secure application behavior:
- Input validation and output encoding.
- Parameterized queries.
- Strong authentication and authorization.
- Secure parsing and schema validation for JSON and XML.
How Jsmon Helps in Real Assessments
Bypassing a WAF with padding only works if you know the exact endpoint and expected parameters. Jsmon accelerates this reconnaissance by parsing JavaScript bundles to give you the exact blueprint needed for your attack.
- Uncovering Hidden Endpoints: Jsmon finds undocumented APIs (like
/v1/bulk-upload) that administrators often forget to secure with strict WAF inspection limits. - Building Valid Payloads: It extracts the exact JSON keys the backend expects, ensuring your padded request is actually processed by the server instead of throwing a syntax error.
- Finding Large-Body Targets: Spotting client-side validation logic in Jsmon (like checking for a 10MB file limit) is a massive hint that the server accepts large bodies, making it the perfect target for a padding bypass.
Conclusion
Payload padding is a reminder that WAFs are optimized systems with hard limits. Many bypasses are not “magic.” They are the natural outcome of performance constraints meeting permissive defaults.
If you are testing a target protected by a WAF, don’t jump straight to exotic encodings. First, measure the inspection boundary and try a controlled padding approach.
If you are defending a production system, assume attackers will do the same. Configure oversize handling to fail closed, tune inspection limits thoughtfully, and use endpoint-specific policies so the security control behaves predictably under pressure.
References
- https://youtube.com/shorts/O84bLLJK_iI?si=O5kdvo139BEXq15a
- https://youtu.be/0OMmWtU2Y_g?si=HdSlMaF4gvjEY7ri
- https://docs.aws.amazon.com/waf/latest/developerguide/limits.html
- https://docs.aws.amazon.com/waf/latest/developerguide/web-acl-setting-body-inspection-limit.html
- https://github.com/assetnote/nowafpls



