Cybercrime-as-a-Service: The Industrialization of the Threat Landscape

The first time a LockBit affiliate logged into an admin panel, configured a ransomware build, and deployed it against a target network without writing a single line of code, something fundamental changed in the threat landscape. That affiliate was not a developer. They were, in practical terms, a subscriber, operating within a service economy that had quietly professionalized organized cybercrime into something structurally indistinguishable from a SaaS business.
Cybercrime-as-a-Service (CaaS) is the commercialization of offensive cyber capabilities through subscription-based and pay-per-use models, transacted primarily across dark web marketplaces, invite-only underground forums such as XSS.is and Exploit.in, and encrypted messaging platforms including Telegram. Vendors develop and maintain attack toolkits; customers deploy them. Payments flow through cryptocurrency, predominantly Bitcoin and Monero, and escrow systems enforce transactional integrity. What was once the exclusive domain of technically proficient actors is now accessible to anyone with a budget and intent.
Ecosystem Structure
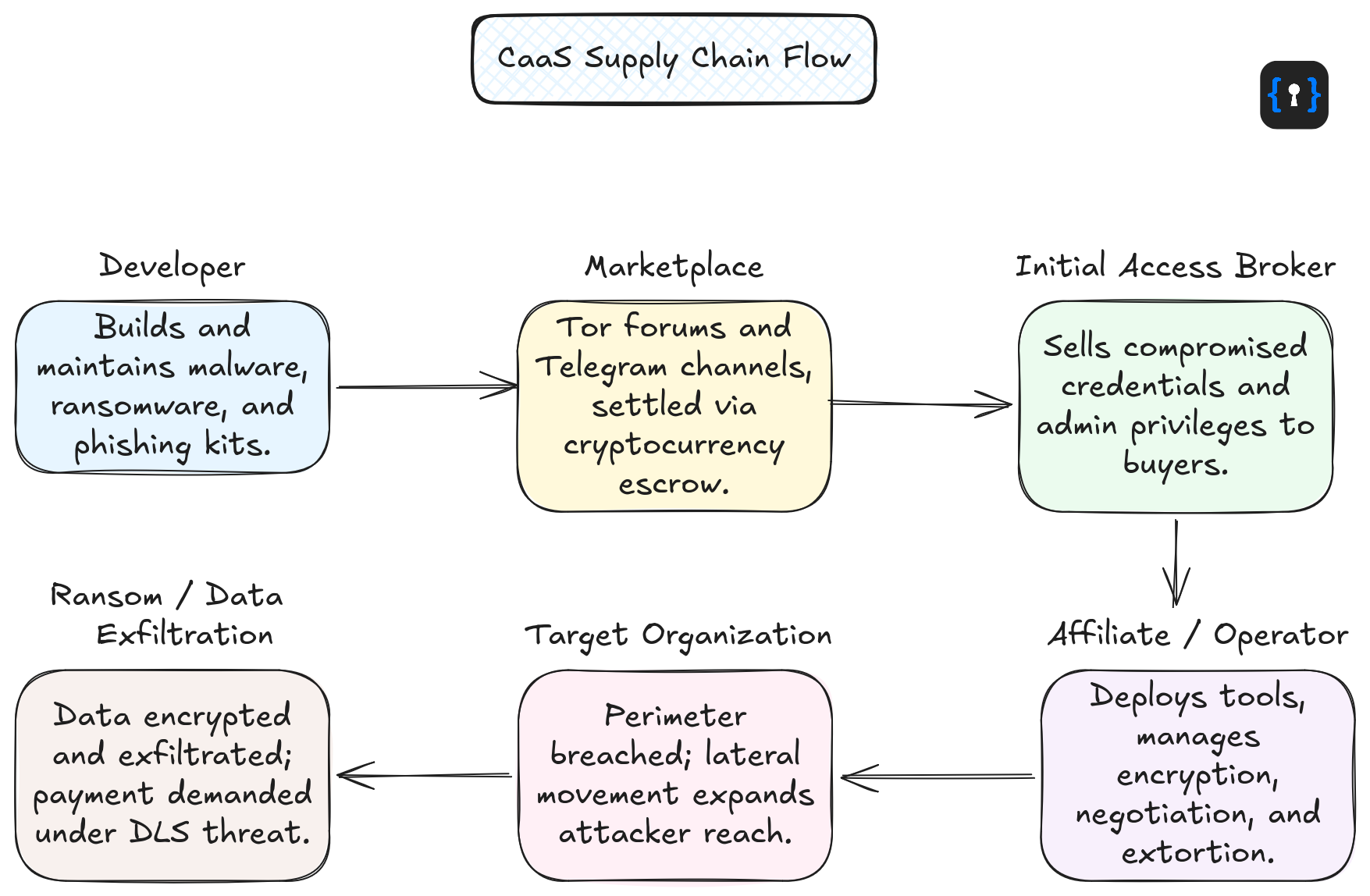
The CaaS supply chain operates through three functionally distinct layers.
Developers constitute the production layer: they engineer ransomware strains, infostealer binaries, phishing kits, exploit packages, and botnet infrastructure, then make these available through dark web storefronts or private channels. In mature operations, development follows versioned release cycles with documented changelogs, consistent with commercial software practices. Lumma Stealer (LummaC2), tracked by Microsoft Threat Intelligence as Storm-2477, has been documented through at least six major versions, each introducing changes to C2 communication protocols, URI path formats, and antivirus evasion logic.
Initial Access Brokers (IABs) specialize in organizational perimeter compromise and monetize the resulting access rather than deploying post-compromise payloads themselves. Inventory sold on underground forums includes VPN credentials, RDP sessions, corporate email accounts, and Active Directory admin privileges, with pricing typically ranging from USD 1,000 to USD 50,000 per listing depending on organizational profile and privilege level. Per the Europol Spotlight report on Crime-as-a-Service, IABs are identified as among the most consequential enablers in the broader CaaS ecosystem, directly supporting ransomware groups, data extortion operations, and nation-state actors alike.
Affiliates and operators represent the deployment layer. They acquire access from IABs, lease tools from the developer layer, and execute attacks against target environments. In Ransomware-as-a-Service (RaaS) models specifically, affiliates subscribe to an operator's platform and handle deployment autonomously, while the platform operator manages victim payment infrastructure, negotiation support, and data leak site administration. Commission structures in observed RaaS programs range from 20 to 40% for entry-level affiliates to up to 80% for those with consistently high attack success rates, as documented in Europol's CaaS report.
Ransomware-as-a-Service
RaaS is the most operationally mature and financially significant CaaS vertical. The model sees technically skilled criminal groups develop and maintain ransomware strains, then package them with supporting infrastructure, including command-and-control servers, victim payment portals, dedicated data leak sites (DLS), and in many cases affiliate management dashboards, and offer the full package under subscription arrangements.
LockBit's operational history illustrates the ceiling of RaaS maturity. LockBit 2.0, first observed in June 2021, provided affiliates with a web-based management panel for victim tracking, ransomware build generation, and decryptor issuance. The group developed StealBit, a proprietary data exfiltration utility that uploaded compressed victim data directly to the LockBit DLS, removing dependency on third-party cloud services that victims could disrupt via abuse complaints. By May 2022, LockBit 2.0 accounted for 46% of all tracked ransomware breach events. Affiliates were required to demonstrate proficiency with tools including Metasploit and Cobalt Strike, a qualification threshold higher than most comparable RaaS platforms, indicating deliberate quality control in affiliate recruitment. LockBit operators also used ransomware notes to recruit organizational insiders, offering "millions of dollars" to employees willing to provide VPN credentials, RDP access, or facilitate an infection manually.
Following Operation Cronos in February 2024, which disrupted LockBit infrastructure, RANSOMHUB launched in early 2024 and emerged as the most prolific DLS by the second half of that year. Mandiant's M-Trends 2025 report identifies RANSOMHUB as tied for the most frequently observed ransomware family in incident response engagements conducted in 2024, with multiple tracked threat clusters, including UNC2165, UNC3944 and UNC5227, assessed to have utilized the platform. The velocity with which RANSOMHUB filled the operational vacuum left by LockBit's disruption is consistent with a market in which affiliate demand consistently outpaces enforcement capacity.
Mandiant's report further notes that brute-force attacks, including password spraying against VPN devices, RDP login attempts at high volume, and exploitation of default credentials, represented the most commonly identified initial infection vector for ransomware-related intrusions in 2024. Stolen credentials and software exploitation were each tied for second at 21%, followed by prior compromise at 15% and third-party compromise at 10%. Of tooling observed across ransomware intrusions, 37% were utilities such as PsExec, 18% were credential stealers, 12% were remote access and administration tools, and 11% were reconnaissance utilities, a profile dominated by commercially available and living-off-the-land tooling that blends with legitimate administrative activity.
Malware-as-a-Service
Darktrace's 2024 Annual Threat Report assessed that Malware-as-a-Service now accounts for 57% of all observed cyber threat campaigns against organizations, up from 40% in the first half of 2024, a 17-percentage-point increase within a single calendar year. MaaS encompasses a broad category including trojans, keyloggers, spyware, and credential-harvesting infostealers, the last of which has become a particularly high-volume segment due to its role in feeding the IAB supply chain.
Lumma Stealer is assessed as among the most operationally active infostealer MaaS offerings as of early 2026. The platform, maintained by Storm-2477, enables affiliates to harvest browser-stored credentials, cryptocurrency wallet data, two-factor authentication tokens, and session cookies. Ransomware operators including Octo Tempest, Storm-1607, Storm-1113, and Storm-1674 have been observed deploying Lumma Stealer as an initial access or credential-harvesting component in broader attack chains, illustrating how MaaS and RaaS verticals interact within the same intrusion.
Lumma Stealer's delivery infrastructure demonstrates the multi-vector distribution characteristic of mature MaaS operations. Observed delivery methods include malvertising campaigns targeting software download queries (e.g., "Notepad++ download"), drive-by downloads executed via compromised websites injecting malicious JavaScript, trojanized application packages distributed through file-sharing platforms, and abuse of GitHub for payload hosting. A particularly prominent delivery method is ClickFix, a social engineering technique in which victims encounter fake CAPTCHA pages and are instructed to paste malicious commands into the Windows Run dialog. In a campaign observed in April 2025 targeting Canadian organizations, the attack chain incorporated the Prometheus traffic direction system (TDS) hosted on compromised sites, routing targets through a ClickFix framework that ultimately delivered Lumma Stealer alongside XWorm malware. This activity did not result from product vulnerabilities; the infection chain relied on social engineering and systematic abuse of legitimate infrastructure.
Phishing-as-a-Service
Phishing remains among the most volume-intensive attack vectors in the observed record. Darktrace detected more than 32 million phishing emails across its customer base in 2025. The scale of the problem is reflected across the broader email ecosystem, where Gmail reports blocking over 100 million phishing messages every day. According to Kaspersky, more than 144 million malicious or unwanted email attachments were identified in 2025, while analysis from Palo Alto Networks’ Unit 42 found that 23% of all intrusion cases began with phishing as the initial access vector. Phishing-as-a-Service (PhaaS) platforms have materially lowered the technical floor for conducting large-scale, multi-tenant campaigns, and in the most capable offerings, enabled bypasses of commonly deployed multifactor authentication methods.
Tycoon2FA, tracked by Microsoft Threat Intelligence as Storm-1747 and first observed in August 2023, is illustrative. The platform provided adversary-in-the-middle (AiTM) capabilities: by proxying authentication flows, it intercepted session cookies generated during MFA completion, granting attackers persistent access to compromised accounts without requiring the victim's password following initial compromise. Subscriptions started at USD 120 for 10-day panel access and USD 350 per month. The customer-facing admin panel centralized campaign configuration, lure template selection, redirect routing, CAPTCHA behavior, and victim tracking, including real-time monitoring of captured credentials and session tokens exfiltrated via Telegram bot.
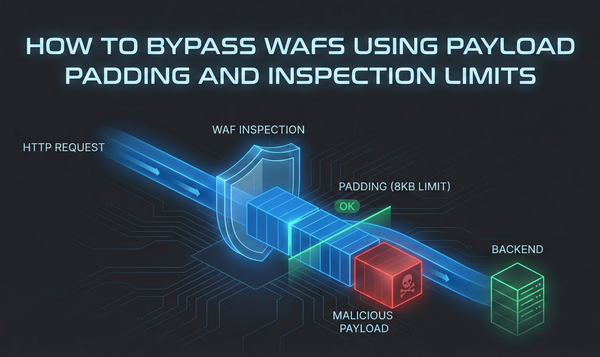
Infrastructure rotated across fully qualified domain names (FQDNs) typically active for 24 to 72 hours, leveraging inexpensive generic TLDs (.space, .email, .solutions, .live) and Cloudflare Workers-based intermediary URLs to complicate blocklist-based defenses. Anti-analysis measures included browser fingerprinting, randomized HTML5 canvas CAPTCHA challenges, non-functional dead code injection to defeat consistent fingerprinting, geolocation filtering, and decoy page substitution when automated analysis environments were detected. Tycoon2FA's capability to bypass SMS one-time passcodes, authenticator app codes, and push notifications is a direct indicator of the inadequacy of these MFA implementations against AiTM-capable PhaaS platforms.
Underground Market Economics
CaaS platforms have adopted operational structures closely mirroring legitimate SaaS marketplaces: vendor vetting processes, buyer-facing reputation ratings, tiered subscription pricing, escrow-enforced transactions, and dedicated support channels. Escrow is a standard practice for transactions, with funds held in forum-controlled wallets until delivery is confirmed. Disputes are settled by moderators with access to chat logs and transaction records. Platform administrators generate revenue through advertising, VIP membership tiers, and transaction fees of 5 to 15% per deal.
Pricing across observed CaaS verticals reflects a functional market: DDoS-as-a-service offerings have been observed starting at USD 20 per month for botnet rental; entry-level PhaaS subscriptions at USD 50 per month; and premium RaaS platforms ranging from USD 40 to several thousand dollars per month. The average ransom demand in 2025 was USD 1.3 million, a figure that contextualizes why even modestly priced RaaS subscriptions generate meaningful returns for affiliates without requiring every attack to succeed.
Defensive Priorities
Given the structural accessibility of CaaS infrastructure, the threat population is no longer bounded by technical expertise. An affiliate operating a mature RaaS platform with commercially available tooling can produce outcomes operationally indistinguishable from a technically expert actor. Defensive programs must account for this.
- Enforce phishing-resistant MFA. FIDO2/passkey-based authentication does not transmit interceptable codes and provides materially higher assurance against AiTM-capable PhaaS platforms such as Tycoon2FA. SMS OTP, authenticator app codes, and push notifications should not be treated as sufficient controls for high-value accounts.
- Implement account lockout and MFA registration controls. Brute force attacks remain one of the leading ransomware initial access vectors. Locking accounts after repeated failed login attempts, enforcing verification for remote first time MFA enrollment, and applying strict rate limiting directly disrupt this intrusion path.
- Monitor dark web and underground forums. CaaS intrusions frequently involve IAB precursor activity, including the listing of organizational credentials on underground marketplaces. Proactive threat intelligence monitoring provides advance warning of targeting before an active intrusion begins.
- Enforce network segmentation and least-privilege access. Lateral movement following initial access is a consistent feature of RaaS intrusion patterns. Segmentation that limits blast radius from a single compromised endpoint reduces the attacker's ability to escalate to domain-wide ransomware deployment.
- Patch internet-facing infrastructure on a priority basis. VPN vulnerability exploitation remains one of the primary initial access vectors for ransomware operations. Timely patching of VPN appliances and remote access gateways directly reduces initial access broker viability against organizational perimeters.
- Exercise multi-vector incident response scenarios. CaaS operators are not constrained to single-technique campaigns. Tabletop exercises should simulate concurrent phishing, credential stuffing, and ransomware deployment within the same timeline, reflecting observed operational patterns.
Could Your Attack Surface Be Jsmon's Next Alert?
Your perimeter controls mean nothing if access credentials are already exposed in your JavaScript. Jsmon gives security leaders continuous visibility into the codebase vulnerabilities that CaaS operators actively monetize, before your organization becomes a case study.