CVE-2026-27825 Explained: Unauthenticated RCE in Atlassian MCP Servers
The Model Context Protocol (MCP) is quickly becoming the connective tissue between modern AI assistants and enterprise systems. Instead of being limited to a static knowledge base, an AI agent can use an MCP server to fetch Jira issues, read Confluence pages, summarize internal documentation, and even take actions across workflows. That convenience is also exactly what makes MCP servers high-value targets: they sit at the boundary between external requests and privileged internal APIs, and they often run with access that attackers would love to inherit.
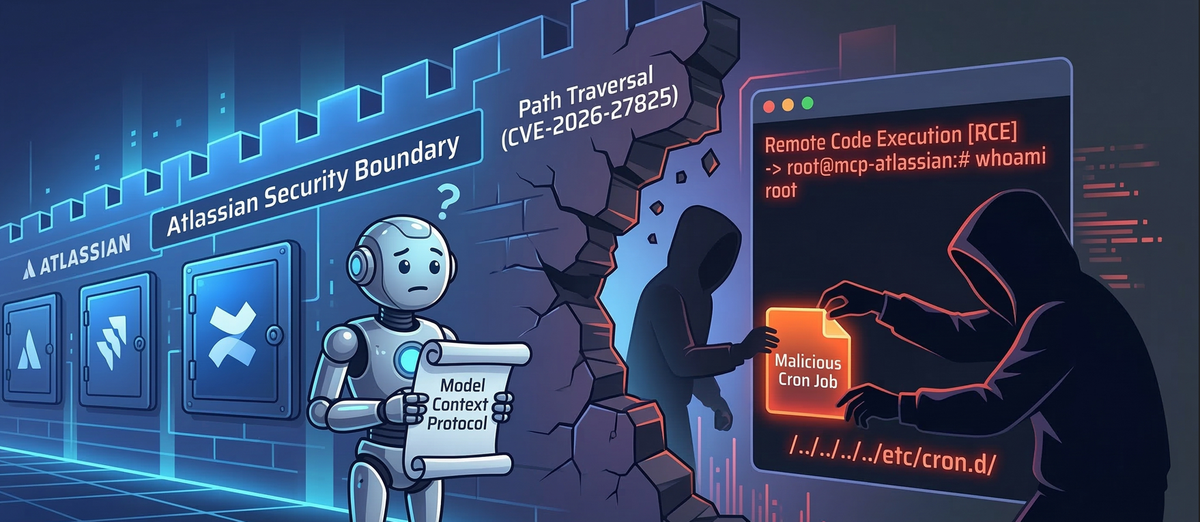
In March 2026, researchers disclosed two critical vulnerabilities in mcp-atlassian, a widely used open-source MCP server developed by sooperset. Individually, each bug is serious. Chained together, they become the kind of “small mistakes → catastrophic outcome” story security teams dread: an unauthenticated, network-adjacent attacker can abuse a middleware SSRF to bypass trust boundaries and then leverage an arbitrary file write (path traversal) to land persistence and achieve remote code execution.
This article walks through the vulnerabilities, how the exploit chain works in practice, and what defenders should do to harden MCP deployments.
MCP servers are built to mediate between an AI agent and enterprise systems. In an Atlassian context, that usually means Jira and Confluence. At a high level, the MCP server:
- Accepts tool invocation requests (for example, “get current Jira user” or “download Confluence attachment”).
- Authenticates the request or trusts a calling environment (depending on deployment).
- Calls internal or external Atlassian APIs.
- Returns the results to the agent.
That is a powerful role. If the MCP server is tricked into calling attacker-chosen endpoints (SSRF), or writing attacker-chosen files (arbitrary write), it effectively becomes an attack proxy with the privileges of the service account and the host it runs on.
Critical Vulnerability Analysis: The Danger of Chained Flaws
The disclosed chain centers on two CVEs:
- CVE-2026-27826: a Server-Side Request Forgery (SSRF) flaw in the server’s middleware logic.
- CVE-2026-27825: an arbitrary file write via path traversal in the Confluence attachment download logic (CVSS 9.1).
The key idea is simple but devastating:
- SSRF gives the attacker control over where the server makes outbound HTTP requests.
- Arbitrary file write gives the attacker control over where downloaded content is written on disk.
- Put them together, and the attacker can host a malicious “attachment” and force the server to fetch and write it into a sensitive location like
authorized_keysor/etc/cron.d/.
That turns a data-layer integration service into a foothold on the underlying machine.
Stage 1: Middleware SSRF (CVE-2026-27826)
The SSRF originates in the ASGI middleware of the MCP server, specifically called out as being in:
src/mcp_atlassian/servers/main.py
To support different Atlassian deployments, including on-prem instances, the middleware accepts custom base URLs for Jira and Confluence. The intention is reasonable: not every organization uses Atlassian Cloud.
The problem is how the server behaves when a standard Authorization header is not present. In that scenario, the middleware falls back to trusting custom headers such as:
X-Atlassian-Jira-UrlX-Atlassian-Confluence-Url
Those headers are treated as authoritative without sufficient validation.
When a tool is invoked, the dependency injection layer (for example get_jira_fetcher) extracts the URL from request state and immediately performs an outbound request such as get_current_user_account_id() to “verify connectivity.”
That means an attacker can induce outbound requests simply by invoking a tool call while controlling the base URL via headers.
A simplified example targeting AWS metadata (IMDS) looks like this:
POST /v1/tools/call HTTP/1.1
Host: mcp-internal.company.local
X-Atlassian-Confluence-Url: <http://169.254.169.254/latest/meta-data/iam/security-credentials/>
Content-Type: application/json
{"name": "get_current_user", "arguments": {}}
This SSRF is not “just” a backend calling a random URL. It enables at least two major outcomes:
- Internal network access The server becomes a proxy to:
- Query metadata services (like AWS IMDS at
169.254.169.254). - Probe internal services that are not internet-accessible.
- Perform port scanning or service enumeration from a trusted network segment.
- Query metadata services (like AWS IMDS at
- AI context poisoning and prompt injection delivery If the attacker points the server to an attacker-controlled endpoint that mimics Atlassian API responses, the MCP server may ingest fake Jira/Confluence content. That content can be crafted to include hidden instructions intended to manipulate the AI agent’s behavior.
In other words, SSRF here can be both an infrastructure compromise vector and an AI safety failure mode.
Stage 2: Arbitrary File Write via Attachment Download (CVE-2026-27825)
This bug sits in the Confluence attachment handling logic:
src/mcp_atlassian/confluence/attachments.py
The vulnerable functionality is the confluence_download_attachment tool.
The tool allows an AI agent to download a Confluence attachment to a local path. The design assumes that download_path is a harmless location, like a workspace download directory.
However, the vulnerability arises because download_path is accepted from user input and is not properly sanitized against:
- Directory traversal sequences (
../) - Absolute paths (
/etc/...)
A representative abuse payload
{
"name": "confluence_download_attachment",
"arguments": {
"attachment_id": "malicious_payload_id",
"download_path": "../../../../../../../home/mcpuser/.ssh/authorized_keys"
}
}
If the server runs with permissions that allow writing to the target location, the attachment’s contents will be written there. At that point, you no longer have “just a file write bug.” You have a way to plant keys, cron jobs, service definitions, or other persistence artifacts.
The Exploit Chain: Achieving Unauthenticated Host Compromise
On their own:
- SSRF is often used for data access and internal recon.
- Arbitrary file write is often used for persistence or RCE if you can control file content.
The chain combines both: SSRF can give you a controlled content source, and file write places it somewhere powerful.
Technical Kill Chain: Bypassing Security Boundaries
- Attacker hosts a malicious server that imitates Atlassian endpoints and serves a “fake” Confluence attachment. The attachment content might be:
- An SSH public key
- A reverse shell payload
- A cron entry
- Any content suitable for the target system
- Attacker triggers SSRF using
X-Atlassian-Confluence-Urlto point the MCP server at the attacker infrastructure. - Attacker invokes
confluence_download_attachmentand setsdownload_pathto a sensitive OS file path such as:~/.ssh/authorized_keysfor persistent SSH access/etc/cron.d/malicious-jobto run code as root on a schedule
- Server fetches attacker-controlled content and writes it to the chosen path.
Remote Code Execution: Turning Data Access into System Control
- Writing to
authorized_keyscan give immediate, silent access (assuming SSH is reachable and the target account is valid). - Writing into
/etc/cron.d/can yield root execution within a minute, depending on the payload and system configuration.
In other words, the MCP server is transformed into a remote implant mechanism.
Patch Analysis: How to Mitigate CVE-2026-27825 and CVE-2026-27826
The maintainers patched both issues in version 0.17.0. The fixes are notable because they reflect two foundational security lessons: validate all network destinations (SSRF defense) and enforce filesystem boundaries (path safety).
SSRF mitigation: validate_url_for_ssrf
The patch introduces a URL validation routine that resolves hostnames and blocks access to high-risk destinations, including:
- Loopback (
127.0.0.0/8) - Private networks (
10.0.0.0/8,192.168.0.0/16, etc.) - Link-local metadata endpoints (
169.254.169.254)
This is the right direction. To be effective, SSRF defenses must be done before storing or using the URL, and ideally must include DNS resolution defenses (to reduce bypass via DNS rebinding or tricky hostname encodings).
File write mitigation: validate_safe_path
To fix traversal, the patch adds a safe-path validator that:
- Resolves the absolute path of the user-provided
download_path. - Ensures the result remains within an intended base directory.
- Rejects paths that escape via
../or absolute path tricks.
This “must stay inside a designated folder” rule is one of the most reliable patterns for preventing traversal-based writes.
Security Hardening Guide: Protecting MCP Servers Beyond the Patch
Upgrading is mandatory, but patching alone should not be your only defense. MCP servers are integration hubs, and integration hubs deserve layered controls.
1. Upgrade immediately
Run mcp-atlassian 0.17.0 or later. If you cannot upgrade quickly, treat the server as potentially compromised and consider taking it offline until mitigations are in place.
2. Treat MCP servers as privileged infrastructure
Even if the service “only” pulls Jira and Confluence content, it often:
- Holds credentials or API tokens.
- Has network reachability into internal systems.
- Writes data locally for caching or downloads.
Assume compromise impact is high.
3. Containerize with meaningful restrictions
If you run MCP servers in containers, make the container boundaries real:
- Use a read-only root filesystem where feasible (
--read-only). - Mount only a dedicated writable directory for attachments.
- Drop Linux capabilities.
- Run as a non-root user.
- Use seccomp and AppArmor/SELinux where possible.
4. Enforce strict egress controls
SSRF becomes dramatically less useful when outbound traffic is restricted:
- Allowlist only expected Atlassian domains or on-prem IP ranges.
- Block link-local, metadata IPs, and RFC1918 ranges unless explicitly needed.
- Consider using an outbound proxy with policy controls and logging.
5. Assume AI context is hostile input
Even without SSRF, any external content that reaches an AI agent can carry prompt injection. Practical steps include:
- Clear separation between “retrieved content” and “instructions.”
- Tool-level authorization checks that do not rely on the model’s judgment.
- Logging and review of tool calls triggered by untrusted content.
6. Audit middleware and pre-tool call behavior
The SSRF here is a classic example of a dangerous pattern:
“Make outbound requests early, before full validation, because it’s convenient for connectivity checks.”
Any new integration layer should be reviewed for:
- Where user-controlled URLs enter the system.
- When outbound calls occur.
- Whether authentication can be bypassed via alternate headers or fallback logic.
Conclusion
The chained Atlassian MCP vulnerabilities (CVE-2026-27826 and CVE-2026-27825) are a clear warning shot for the AI integration era. As organizations rush to connect LLMs to internal systems, MCP servers become powerful gatekeepers. If that gatekeeper can be tricked into calling attacker-controlled URLs and writing attacker-controlled files, the result is not just data leakage or AI misbehavior. It is a direct path to host-level compromise.
The immediate action is straightforward: upgrade mcp-atlassian to 0.17.0+. The broader lesson is equally important: MCP servers should be built and operated like high-risk middleware. Validate all network destinations, confine filesystem access, restrict egress, and assume any content reaching the model can be weaponized.
That combination, more than any single patch, is what will keep “helpful internal assistants” from becoming the attacker’s favorite entry point.
References & Further Reading
- Miggo Security Root Cause Analysis:
- Pluto Security Technical Blog: MCPwnfluence: CVE-2026-27825 Critical Vulnerability
- Arctic Wolf Threat Report: CVE-2026-27825 Critical Unauthenticated RCE and SSRF in MCP Atlassian
- Vulnerability Tracking & Advisories: