CVE-2026-20805 Explained: Understanding Windows Memory Leaks and KASLR Bypasses
Modern security conversations still revolve around the familiar greatest hits: SQL injection, cross-site scripting, exposed admin panels, and the steady stream of web flaws that dominate headlines and bug bounty write-ups. Those issues matter. But they are no longer the whole story.
Advanced threat actors are increasingly aiming lower in the stack and higher in impact, shifting attention from the “surface” to the foundations of enterprise environments. Operating systems. Directory services. Core rendering components. The parts of the platform that every user touches, every day, and that organizations cannot easily stop, patch, or replace without pain.
That shift is why the January 2026 Patch Tuesday zero-day, CVE-2026-20805 (a Windows Desktop Window Manager information disclosure issue), is such an important case study. It reflects a pattern defenders are seeing more often: not just fast exploitation, but a frightening new tempo where attackers are effectively operating with a negative time-to-exploit.
In other words: the exploit is already real, already weaponized, and already in circulation, before most enterprises have even validated the patch, tested compatibility, and scheduled reboots across thousands of systems.
The Rise of Core Infrastructure Vulnerabilities and Exploits
Why Advanced Threat Actors Target Core OS Components
Core OS subsystems are attractive targets because they offer three things at once:
- Ubiquity: The vulnerable component is present across huge portions of the fleet.
- Privilege and proximity: Many core services run with elevated privileges or interact with privileged memory structures.
- Operational resistance: Even when fixes exist, rolling them out quickly can be disruptive and slow.
Unlike many web-layer vulnerabilities, where a WAF rule, a quick config change, or a targeted hotfix can buy time, OS-level patching usually comes with a hard operational cost: downtime, reboots, user disruption, and the risk of breaking critical applications.
Understanding Negative Time-to-Exploit in Cybersecurity
“Negative time-to-exploit” is the moment defenders dread: when adversaries have already built reliable exploit chains, while defenders are still in the early stages of response:
- Patch is announced.
- Proof-of-concept emerges quickly (or exploitation is already observed).
- Enterprises enter a familiar cycle: validate, test, pilot, schedule, reboot.
- Attackers exploit the gap, especially where uptime pressure slows patch velocity.
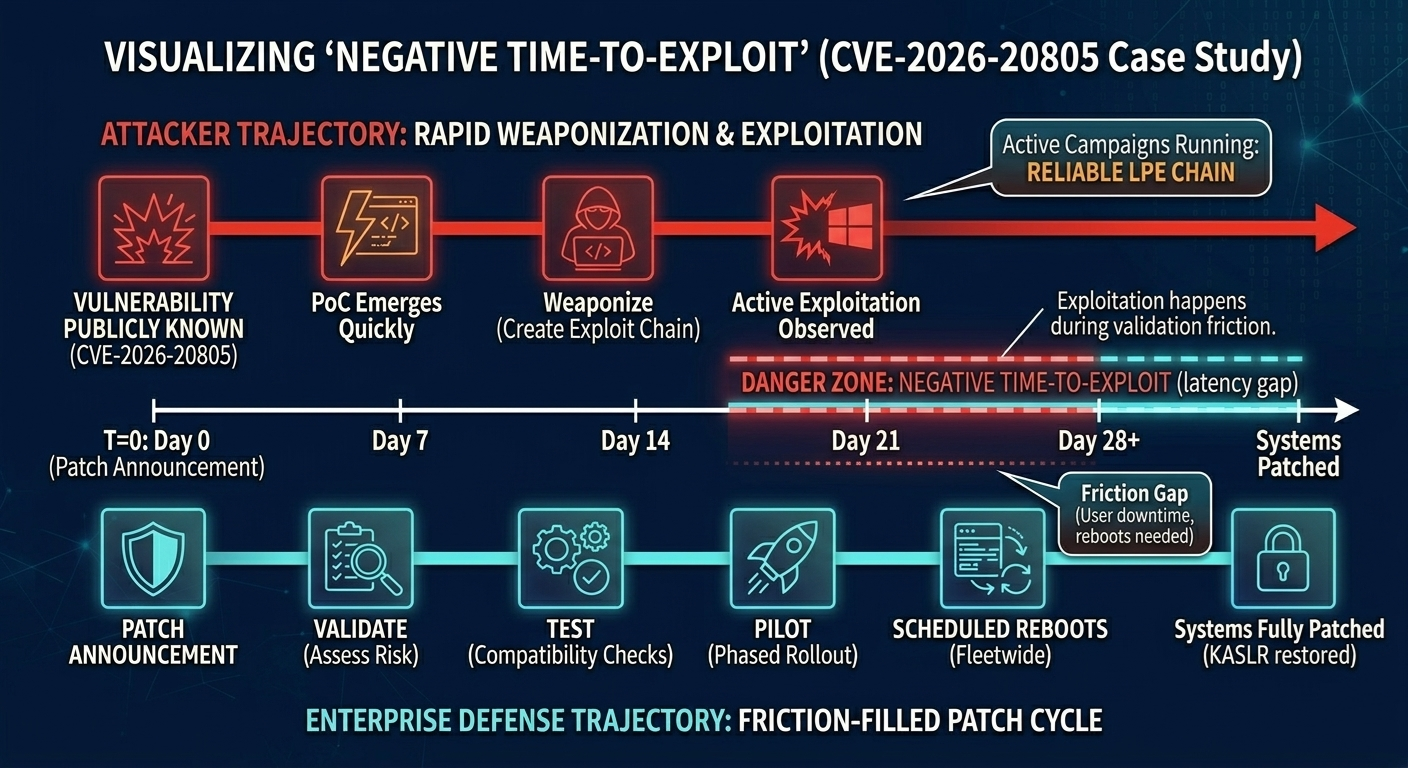
CVE-2026-20805 is a clear anchor for this reality because it is not “just a leak” in isolation. It is the type of bug that can be used to make other exploitation far more dependable.
Understanding CVE-2026-20805
What is DWM (Desktop Window Manager)?
The Desktop Window Manager (dwm.exe) is a core Windows subsystem responsible for composing and rendering the graphical interface. It sits at the center of the user experience, managing how windows are drawn and displayed.
Because it is deeply integrated into the operating system and interacts with low-level rendering and memory structures, it is not a small, isolated process. It is one of those “monolithic giants” in Windows that enterprises depend on, constantly.
Information Disclosure and Memory Leak Vulnerabilities
CVE-2026-20805 is categorized as an Information Disclosure issue, specifically described as a memory leak in how DWM handles crafted object structures.
Information disclosure vulnerabilities can be misunderstood as “less severe” because they do not necessarily provide direct code execution. That framing is dangerously incomplete.
How Information Disclosure Acts as an Exploit Multiplier
On its own, an information disclosure might not hand an attacker a shell. But in modern exploitation, information is often the missing ingredient.
Leaking memory addresses, especially kernel-related pointers, can provide the exact primitive attackers need to defeat exploit mitigations. And once mitigations fall, exploit chains that were previously unreliable become repeatable and weaponizable.
Exploit Mechanics: Building Reliable Exploit Chains
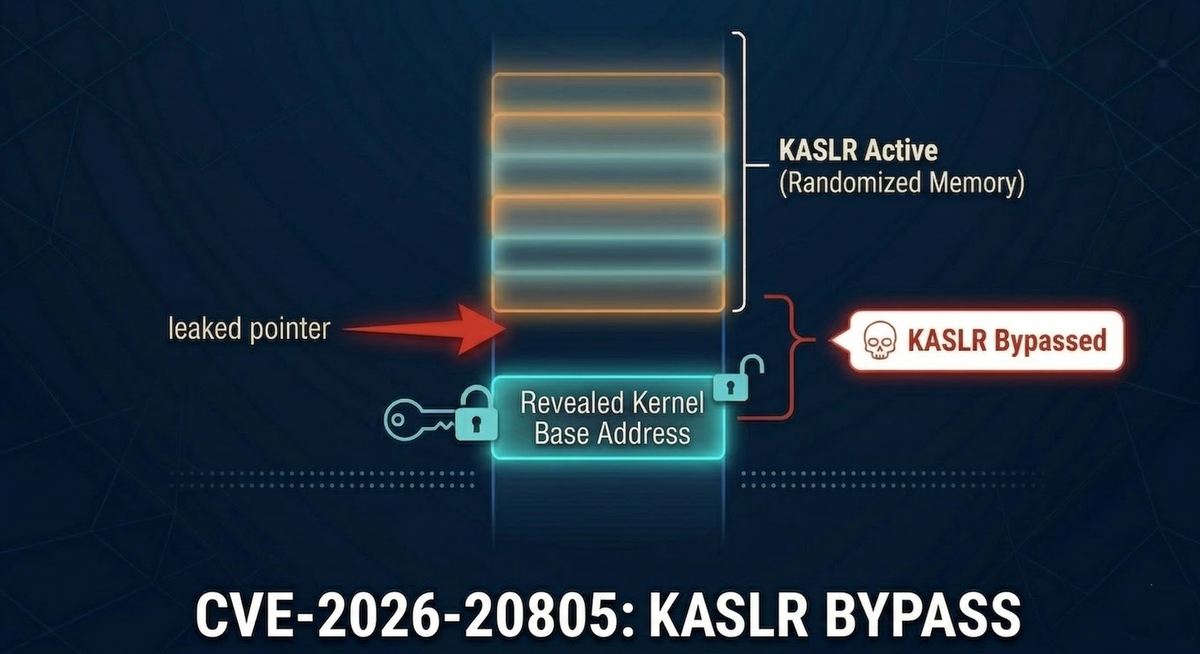
The Role of KASLR in Operating System Security
Modern operating systems deploy multiple mitigation layers designed to break exploit reliability. One of the most important is:
KASLR (Kernel Address Space Layout Randomization): Randomizes where key kernel code and structures are located in memory.
This means that even if an attacker has a working Local Privilege Escalation (LPE) technique, the exploit may still fail unpredictably because the attacker cannot accurately target the right memory addresses.
Without those addresses, many attempts end in instability: crashes, failed exploitation, and sometimes a full system stop (the classic Blue Screen of Death).
Bypassing KASLR Defenses Using Memory Leaks
CVE-2026-20805 fits neatly into a common modern exploit chain pattern:
- Trigger the leak: The attacker sends a malicious payload that causes DWM to mishandle crafted structures.
- Receive a pointer: DWM leaks a kernel pointer (or kernel-adjacent address) back to the attacker.
- Compute the kernel base: The attacker subtracts a known offset, often derived from patch diffing or reverse engineering, to calculate the real base address of
ntoskrnl.exe.
Once the base address is known, the attacker can aim a second-stage exploit far more precisely.
Exploit Development: Offset-Based Base Address Calculation
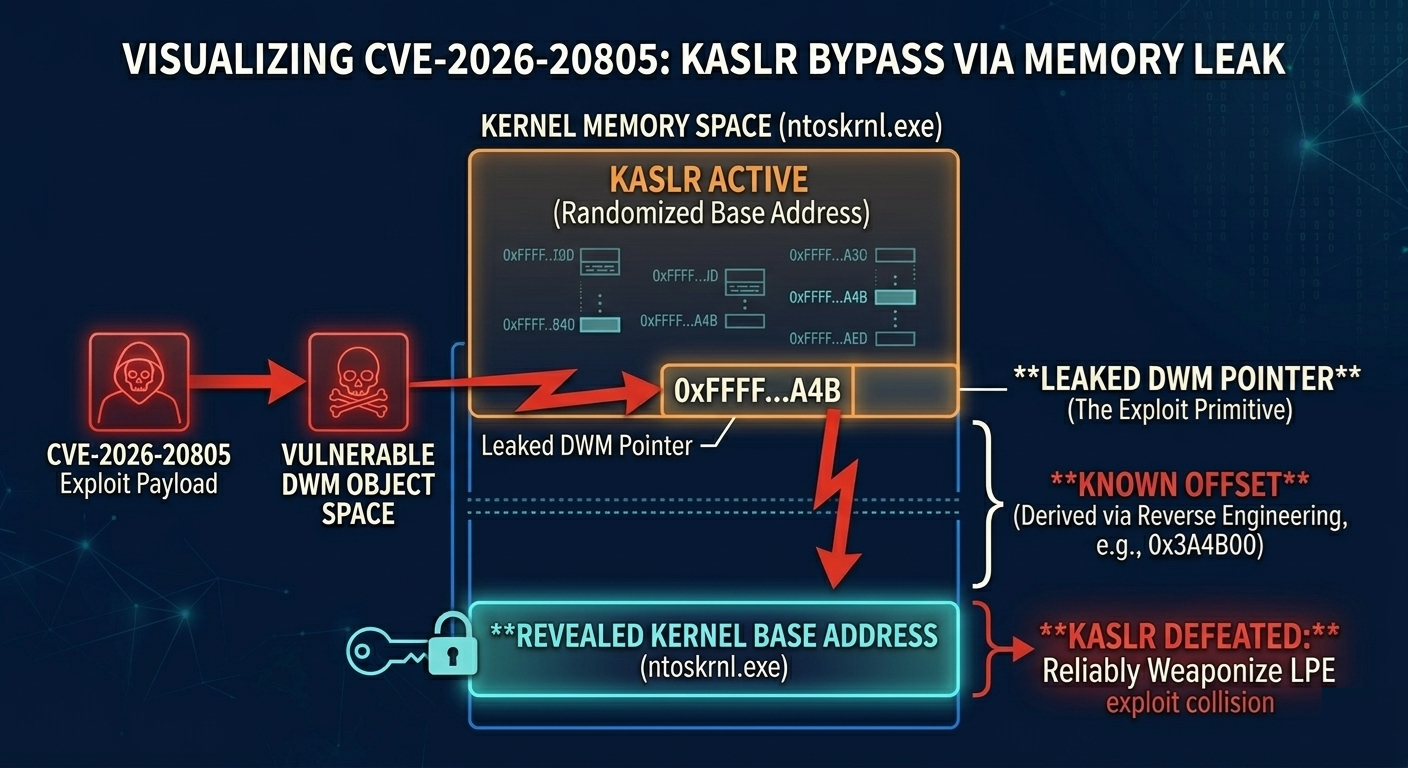
Below is a conceptual snippet illustrating the “leaked pointer → base address” workflow used to neutralize randomization. It is not a drop-in exploit, but it captures the logic defenders need to understand:
// Conceptual snippet: Defeating KASLR using a leaked pointer
#include <windows.h>
#include <stdio.h>
// Assume trigger_dwm_leak() exploits CVE-2026-20805 to return a leaked kernel address
ULONG64 trigger_dwm_leak();
int main() {
printf("[*] Exploiting CVE-2026-20805 to leak DWM memory...\\n");
ULONG64 leaked_address = trigger_dwm_leak();
if (leaked_address == 0) {
printf("[-] Exploit failed. No leak detected.\\n");
return -1;
}
printf("[+] Leaked Kernel Pointer: 0x%llx\\n", leaked_address);
// The offset is found during patch-diffing/reverse engineering
// It represents the distance from the leaked object to the kernel base
ULONG64 kernel_offset = 0x3A4B00;
ULONG64 ntoskrnl_base = leaked_address - kernel_offset;
printf("[+] Calculated ntoskrnl.exe Base Address: 0x%llx\\n", ntoskrnl_base);
printf("[*] KASLR defeated. Proceeding with LPE payload...\\n");
// Attacker now executes the next stage of the exploit chain (e.g., token stealing)
// execute_lpe(ntoskrnl_base);
return 0;
}
Why Exploit Reliability is the Ultimate Attacker Goal
This is the strategic value of CVE-2026-20805. It acts as a reliability multiplier.
Attackers do not always need a single “magic” vulnerability that does everything. They increasingly assemble chains:
- One bug to leak information.
- Another bug to elevate privileges.
- Another technique to persist or move laterally.
If the leak makes LPE exploitation predictable, then what used to be noisy and fragile becomes stable enough for real campaigns.
Enterprise Patch Management Challenges for OS Vulnerabilities
Even when the fix exists, defenders have to operationalize it, and OS-level patches are rarely painless.
OS Patching Risks: Navigating Deep Infrastructure Dependencies
Core OS components are not like patching a web library. They are woven into:
- Endpoint workflows
- Legacy applications
- Remote access tooling
- Security products
- Virtual desktop environments
- Change management and maintenance windows
When the vulnerable component is central to the desktop experience, patching can create user-impacting side effects that IT teams must test carefully.
The Reboot Penalty: Balancing Security Patches and System Uptime
For many Windows fixes, especially in core subsystems, patching requires reboots. That is where enterprise reality bites:
- Reboots must be scheduled.
- Users resist downtime.
- Some environments cannot restart critical machines quickly.
- Pilots and phased rollouts slow the process.
This creates a predictable window, exactly the window attackers exploit.
How Organizational Friction Accelerates Attack Timelines
At scale, patching is never just a technical task. It is a negotiation between:
- IT Operations, measured by uptime and stability
- Security, measured by risk reduction and incident prevention
When exploitation is active, that friction is not just an inconvenience. It becomes an exposure multiplier.
Active Defense and Mitigation Strategies for Zero-Day Exploits
When a core zero-day is being exploited, the goal is not perfection. The goal is reducing attacker success probability fast, while shrinking blast radius if they succeed anyway.
Immediate triage: prioritize what attackers will use first
Treat patching as a risk-based operation. Prioritize the January 2026 Windows updates for systems that are most likely to be leveraged in a real chain:
- Internet-facing systems
- Endpoints used by high-privilege users
- Machines with broad administrative tooling
- Shared jump boxes and “utility” workstations
This is not about ignoring the rest of the fleet. It is about reducing the chance of the first major foothold turning into full domain compromise.
Behavioral monitoring: watch the second stage, not just the leak
Because CVE-2026-20805 is most powerful as part of a chain, detection should focus on what comes after exploitation:
- Unexpected child processes spawned from
dwm.exe - Unusual token manipulation events
- Privilege escalation signals visible in EDR telemetry
- Process trees and memory access patterns that are inconsistent with normal GUI rendering behavior
The underlying principle is simple: memory leaks are often stealthy. The next action, privilege escalation payload execution, usually isn’t.
Network segmentation: assume compromise and limit the pivot
If an endpoint is compromised, segmentation is what prevents “endpoint compromise” from turning into “enterprise takeover.”
Key practices include:
- Reduce lateral movement paths from user endpoints to domain controllers.
- Enforce strict access boundaries between workstation networks and critical infrastructure.
- Limit administrative access to dedicated, hardened systems.
- Treat identity services as high-value assets with minimal exposure.
Segmentation is not a substitute for patching. It is the seatbelt that matters when patching cannot happen instantly.
Preventing Initial Access with Automated Reconnaissance
CVE-2026-20805 is described as a local Windows exploit, which means attackers typically need a foothold on the machine before they can use it.
This is where perimeter and application visibility still matter.
Jsmon helps reduce the likelihood of that initial foothold by continuously monitoring the external web perimeter. By parsing frontend JavaScript and source maps, jsmon can uncover hidden API routes and unauthenticated endpoints, exactly the kinds of overlooked exposures attackers use to gain initial access and deliver local privilege escalation payloads.
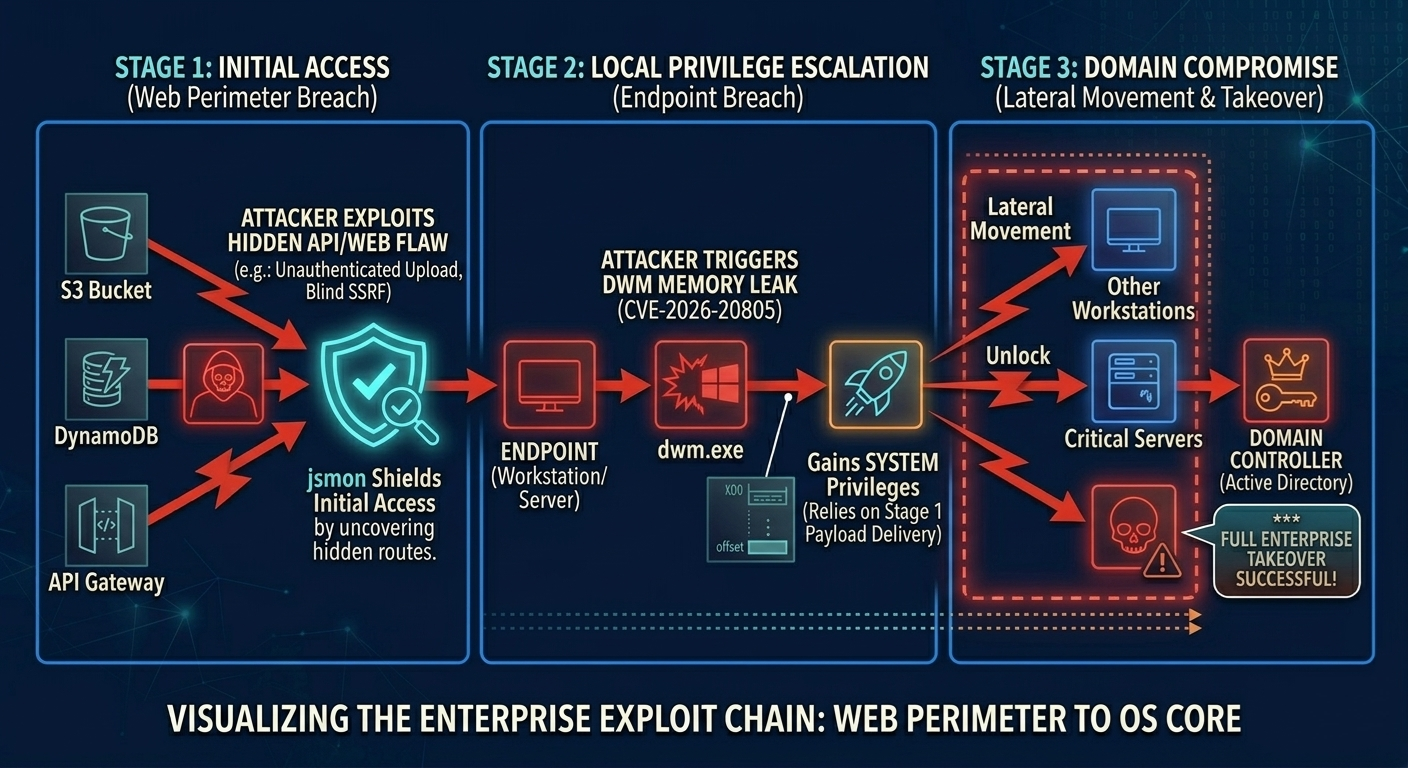
The practical value is straightforward: even if the core OS bug is powerful, the attacker still needs an entry point. Reducing entry points reduces how often the chain can even begin.
Conclusion
CVE-2026-20805 is a reminder that enterprise security is increasingly decided in the “quiet” layers of infrastructure, not just in the loud and familiar web tier.
The exploitation pattern here reflects a broader reality:
- Attackers chain vulnerabilities to build reliable outcomes.
- Information disclosure bugs are not “minor” if they collapse mitigation.
- OS-level patching is operationally hard, so adversaries plan around patch latency.
- Defenders need both speed (patching) and resilience (monitoring, segmentation, access controls).
If the last decade was defined by web application compromise as the dominant narrative, the next phase looks more like sustained pressure on the core: the components enterprises can least afford to stop, and attackers most want to control.
References
- Official Advisory: Microsoft Security Response Center (MSRC) - CVE-2026-20805
- Vulnerability Tracking: CVE.org Record | Wiz.io Database
- Patch Context: Tenable: January 2026 Patch Tuesday Overview
- Technical Exploit Analysis: GitHub: Inside CVE-2026-20805 | Penligent: The DWM Memory Leak Multiplier