cybersecurity
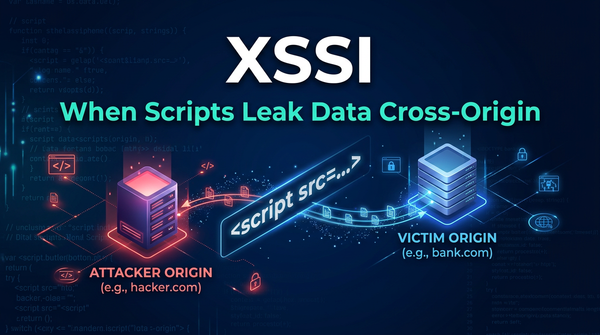
What is Cross-Site Script Inclusion (XSSI)? Ways to Exploit, Examples and Impact
Discover how XSSI works, see real exploitation examples, and learn how to prevent sensitive data leaks in your web apps with this technical guide.
cybersecurity
Discover how XSSI works, see real exploitation examples, and learn how to prevent sensitive data leaks in your web apps with this technical guide.
exposed jenkins instance
Learn how exposed Jenkins instances lead to full system compromise. Explore exploitation techniques and security best practices for your CI/CD pipeline.

backup file exposure
Learn how backup file exposure leads to source code leaks. Explore exploitation techniques, real-world examples, and prevention strategies for .bak files.

ds store file exposure
Learn how .DS_Store file exposure leads to information disclosure. Discover exploitation methods, tools, and how to prevent these leaks on your server.

git directory exposure
Discover how exposed .git folders leak source code and secrets. Learn manual and automated exploitation methods and how to secure your web server today.
dependency confusion attack
Learn how dependency confusion attacks exploit npm and pip. Explore technical examples, exploitation methods, and best practices for prevention.

dangling dns
Discover how dangling DNS records lead to subdomain takeovers. Learn technical exploitation methods and how to secure your attack surface with Jsmon.

subdomain hijacking
Learn how dangling DNS records lead to subdomain hijacking. This technical guide covers exploitation, real-world examples, and mitigation strategies.
cybersecurity
Learn to identify and exploit Memcached unauthenticated access, understand DDoS amplification risks, and implement security best practices for your cache.

cybersecurity
Discover how attackers exploit unprotected MongoDB instances and learn step-by-step technical mitigation strategies to secure your database infrastructure.

cybersecurity
Explore how Redis unauthenticated access leads to RCE and data theft. Learn exploitation methods like SSH injection and critical security mitigations.

cybersecurity
Discover how Firebase database misconfigurations lead to data leaks. Learn to identify insecure rules, exploit scenarios, and prevention tips.