cybersecurity
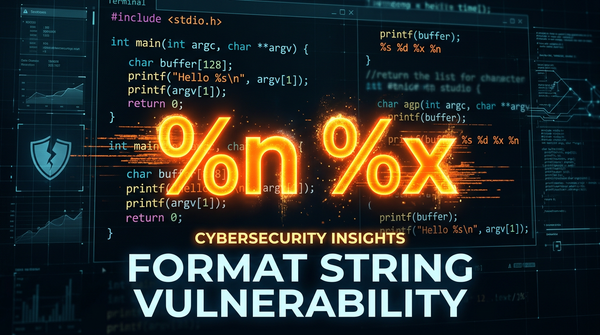
What is Format String Vulnerability? Ways to Exploit, Examples and Impact
Memory corruption vulnerabilities have long been the cornerstone of low-level exploitation. Among these, the format string vulnerability stands out as a classic yet devastating class of bug that occurs when an application improperly filters user input passed into functions like printf(). In this guide, we will explore the mechanics of