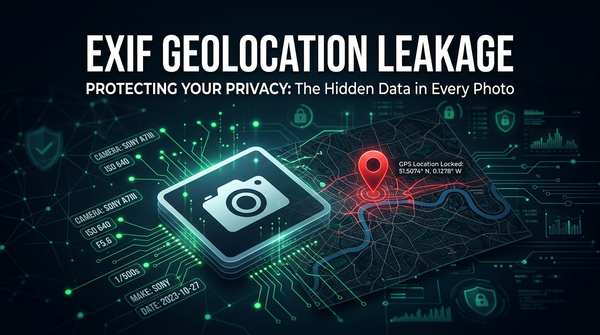
What is Metadata (EXIF) Geolocation Leakage? Ways to Exploit, Examples and Impact
Learn how EXIF metadata leaks GPS data. Explore extraction tools like ExifTool and Python, real-world examples, and mitigation strategies for security.
Learn how EXIF metadata leaks GPS data. Explore extraction tools like ExifTool and Python, real-world examples, and mitigation strategies for security.

403 bypass
Discover how side-channel attacks exploit physical leakage to steal data. Learn about timing attacks, power analysis, and mitigation strategies.

Explore unrestricted file upload vulnerabilities. Learn how attackers use web shells and XSS to compromise servers and how to implement robust security.

Learn about currency rounding vulnerabilities (salami slicing). See how rounding errors lead to financial loss and how to secure your code.
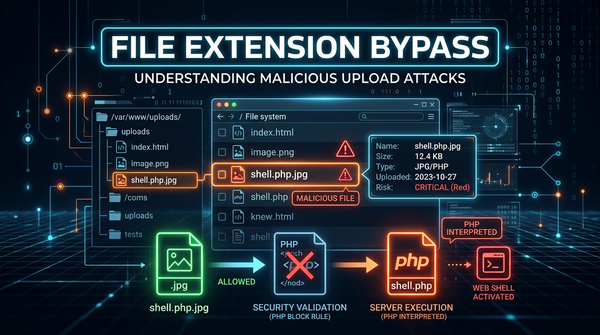
Learn how attackers bypass file extension filters to achieve RCE. Explore common bypass techniques and mitigation strategies to secure your web applications.

Learn how Zip Slip allows RCE via path traversal in archive extraction. See technical examples and learn how to secure your code against this critical flaw.
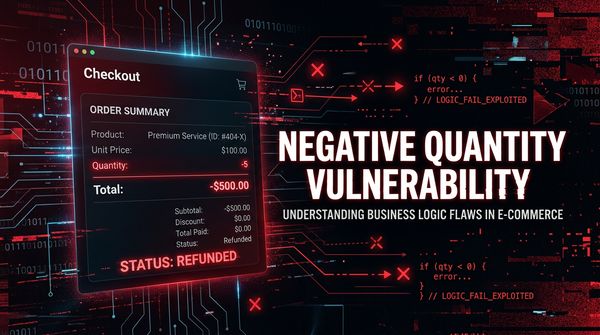
Learn how negative quantity vulnerabilities allow attackers to manipulate e-commerce totals. Explore exploit examples, technical impacts, and prevention tips.
Learn how Pixel Flood attacks exploit image processing to cause DoS. Explore exploitation techniques, real-world examples, and mitigation strategies.

Learn how price manipulation vulnerabilities work, explore real-world exploitation examples, and discover best practices for securing e-commerce platforms.
403 bypass
Learn how the XML Bomb (Billion Laughs) attack works, explore exploitation examples, and find technical ways to prevent this resource exhaustion vulnerability.

Discover how ImageTragick (CVE-2016-3714) works. Learn to exploit and mitigate RCE in ImageMagick with practical examples and security best practices.
Learn how carding attacks work, how attackers use bots to validate stolen cards, and technical ways to protect your business from e-commerce fraud.