
cybersecurity
What is Insecure Deserialization? Ways to Exploit, Examples and Impact
Discover how insecure deserialization leads to RCE. Explore technical examples in PHP and Python, and learn how to secure your infrastructure today.

cybersecurity
Discover how insecure deserialization leads to RCE. Explore technical examples in PHP and Python, and learn how to secure your infrastructure today.
cybersecurity
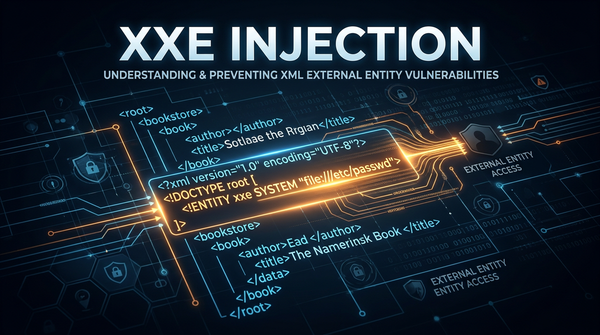
Learn what XXE injection is, how to exploit it with payloads, and how to prevent it. A comprehensive guide for cybersecurity beginners and professionals.
cybersecurity
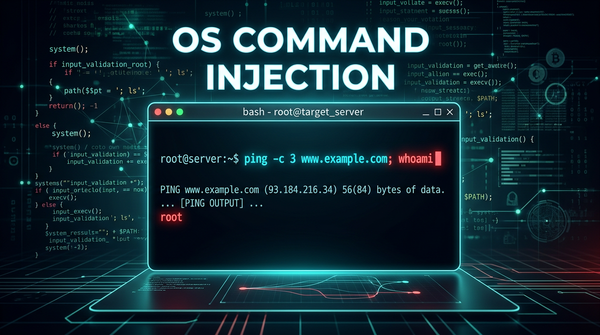
Master the fundamentals of OS Command Injection. Learn how attackers exploit shell vulnerabilities and how to secure your infrastructure with Jsmon.

cybersecurity
Understand Remote Code Execution (RCE) with technical examples of command injection, SSTI, and deserialization. Learn how to secure your systems with Jsmon.

cybersecurity
Learn what Insecure Direct Object Reference (IDOR) is, how to exploit it with technical examples, and best practices for prevention in our deep-dive guide.

cybersecurity
Learn how Blind SSRF works, how to detect it using OAST, and ways to prevent this critical vulnerability from exposing your internal network.

cybersecurity
Master Server-Side Request Forgery (SSRF). Learn how attackers bypass filters, access cloud metadata, and secure your infrastructure against SSRF attacks.
cybersecurity
Understand Cross-Site Request Forgery (CSRF) with technical examples and payloads. Learn how to defend your web applications using modern security practices.
ethical hacking
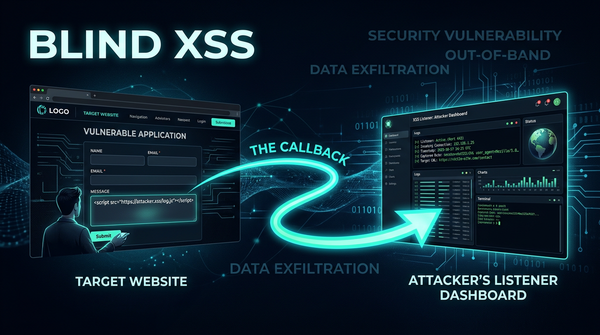
Learn how Blind XSS works, common exploit examples, and impact. Discover how to detect and prevent this dangerous out-of-band vulnerability today.
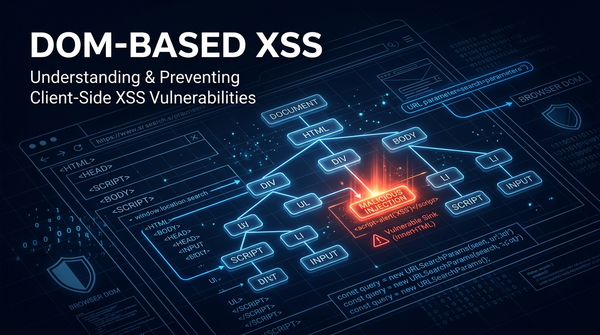
ethical hacking
Learn how DOM-based XSS works, explore technical exploitation examples, and find actionable mitigation strategies to secure your client-side JavaScript.

Cross-Site Scripting
Master Stored Cross-Site Scripting (XSS). Learn technical exploitation techniques, see real-world payloads, and discover how to secure your web applications.
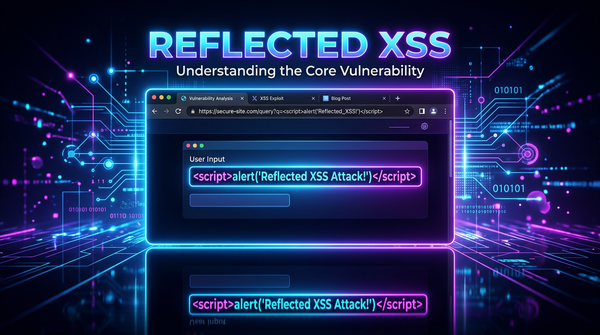
cybersecurity
Understand Reflected Cross-Site Scripting (XSS) with technical examples and payloads. Learn how to detect and mitigate XSS to secure your web applications.