
cybersecurity
What is Excessive Data Exposure in APIs? Ways to Exploit, Examples and Impact
Learn how to identify and prevent Excessive Data Exposure in APIs. Explore technical examples, exploitation methods, and security best practices.

cybersecurity
Learn how to identify and prevent Excessive Data Exposure in APIs. Explore technical examples, exploitation methods, and security best practices.
cybersecurity
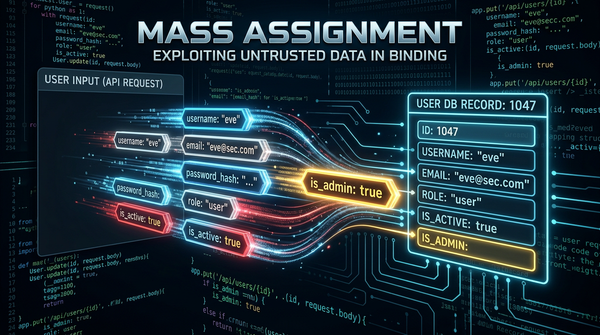
Learn how Mass Assignment vulnerabilities allow attackers to escalate privileges. Explore technical examples and mitigation strategies for secure APIs.

cybersecurity
Learn about Broken Function Level Authorization (BFLA), its impact, and how to prevent this critical API security flaw with technical examples and best practices.
cybersecurity
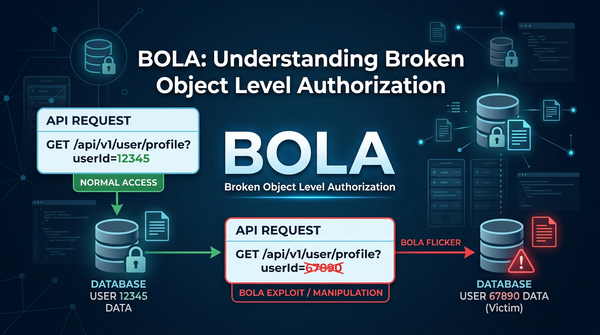
Master Broken Object Level Authorization (BOLA). Learn technical exploitation methods and how to secure your APIs against the #1 OWASP threat.
cybersecurity
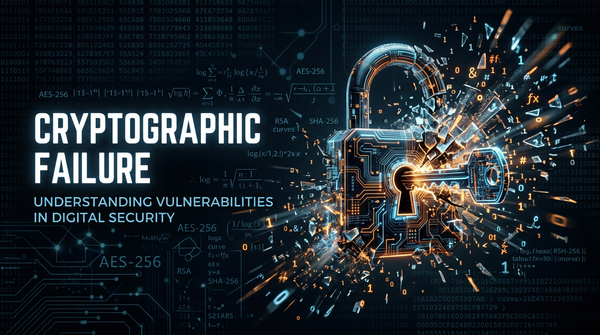
Learn how cryptographic failures happen, explore technical exploit examples, and discover best practices for securing sensitive data in this deep dive.

cybersecurity
Explore the risks of insufficient logging and monitoring. Learn how attackers exploit visibility gaps and how to implement robust security monitoring.

cybersecurity
Explore what security misconfiguration is, see real-world exploitation examples, and learn how to harden your attack surface against these common risks.

cybersecurity
Learn how sensitive data exposure happens, common exploitation methods like MitM and IDOR, and technical steps to prevent data leaks in your organization.

cybersecurity
Discover how broken authentication works, explore technical exploit examples like session hijacking, and learn how to secure your app against identity attacks.
cybersecurity
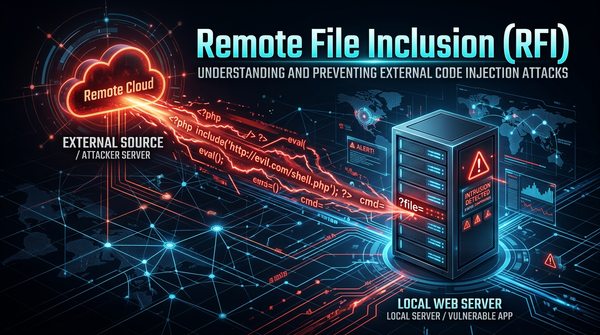
Learn how Remote File Inclusion (RFI) works, see real-world exploitation examples, and discover best practices to prevent RCE attacks on your web server.

cybersecurity
Explore Local File Inclusion (LFI) mechanics, exploitation techniques like path traversal, and practical mitigation strategies for developers.
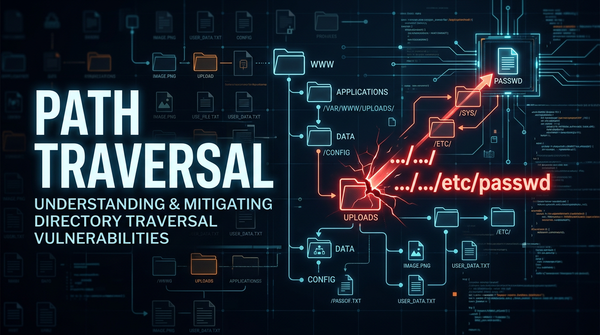
cybersecurity
Discover how Path Traversal vulnerabilities work, see real-world exploitation examples, and learn best practices for prevention and mitigation.